InterKosenCTF 2020 Write-up
はじめに
2020/09/05 ~ 2020/09/06に開催されたInterKosenCTF 2020にチームで参加しました。
チームとしては22問解いて5位でした (191チーム中)。
今回は自分がコンテスト中に解いた4問と終了後に解いた1問のWrite-upを書きます。
Misc
No pressure [335pts, 16solves]
nc misc.kosenctf.com 10002
> nc misc.kosenctf.com 10002 message: KosenCTF encrypted! : qc4CwzFIKN9yLB7t1HeLXFYHFyz/H0eeWB08VryfxnsueLy4Nj8fCh575jQ0A2Ix0dSHDYZSY0saeOehV9Tgn7xwT3rez1znfP8DnDCWxa9B message: ABCDEFGH encrypted! : M0MHUBRRP28gNeygAGA+C/JmzeNsB+PxMRnPjfN8wfmYz85RXJKQ+P8KGOR24JiEhFe812zsOiujSb+H4LIVIFgVwDGSFPFB65A1TrovAgY98lme6w== [snip]
chall.py
from Crypto.Cipher import ARC4 from hashlib import sha256 from base64 import b64encode import zlib import os flag = open("./flag.txt", "rb").read() nonce = os.urandom(32) while True: m = input("message: ") arc4 = ARC4.new(sha256(nonce + m.encode()).digest()) c = arc4.encrypt(zlib.compress(flag + m.encode())) print("encrypted! :", b64encode(c).decode())
アプローチ:zlibで利用されているデータ圧縮アルゴリズム(Deflate)の性質を利用する
この問題で注目すべき処理は下記です。
c = arc4.encrypt(zlib.compress(flag + m.encode()))
flagと入力文字列を連結し、zlibで圧縮した値をRC4で暗号化しています。
zlibとRC4には以下ような特徴があります。
- zlibは入力文字列がflagに内包されていれば、データ圧縮効率が上がる(圧縮結果が小さくなる)
- RC4は平文と暗号文の長さが一致する
つまり、入力文字列がflagに内包されている場合は暗号文が短くなります。
以下は簡単なテストスクリプトです。
from pwn import * from base64 import * r = remote('misc.kosenctf.com', 10002) def send_message(msg): recv = r.recvuntil('message: ') r.sendline(msg.encode()) recv = r.recvline() enc = base64.b64decode(recv.decode().split(' ')[-1].strip()) enc_length = len(enc) print(f'msg: {msg}') print(f'len(enc(msg)): {enc_length}') send_message('Kosen') send_message('KosenCTF{') send_message('KosenCTF*') send_message('NITctf')
msg: Kosen
len(enc(msg)): 81
msg: KosenCTF{
len(enc(msg)): 81
msg: KosenCTF*
len(enc(msg)): 82
msg: NITctf
len(enc(msg)): 84
入力文字列がflagに内包されている場合、暗号文が短くなっていることが分かります。 そのため、flagを1文字ずつ求めていくことが可能です。
以下はソルバになります。
from pwn import * from base64 import * import string flag = 'KosenCTF{' r = remote('misc.kosenctf.com', 10002) while True: for c in string.printable: recv = r.recvuntil('message: ') r.sendline(flag.encode() + c.encode()) recv = r.recvline() enc = base64.b64decode(recv.decode().split(' ')[-1].strip()) enc_length = len(enc) if enc_length == 81: flag += c print(flag) break
KosenCTF{D
KosenCTF{DE
KosenCTF{DEF
KosenCTF{DEFL
KosenCTF{DEFLA
KosenCTF{DEFLAT
KosenCTF{DEFLATE
KosenCTF{DEFLATE_
KosenCTF{DEFLATE_i
KosenCTF{DEFLATE_is
KosenCTF{DEFLATE_is_
KosenCTF{DEFLATE_is_a
KosenCTF{DEFLATE_is_an
[snip]
KosenCTF{DEFLATE_is_an_algorithm_that_combines_LZ77_and_Huffman_coding}
KosenCTF{DEFLATE_is_an_algorithm_that_combines_LZ77_and_Huffman_coding}
Crypto
ciphertexts [201pts, 33solves]
Since there are two ciphertexts, it is easy to solve, isn't it?
n1 = 112027309284322736696115076630869358886830492611271994068413296220031576824816689091198353617581184917157891542298780983841631012944437383240190256425846911754031739579394796766027697768621362079507428010157604918397365947923851153697186775709920404789709337797321337456802732146832010787682176518192133746223 n2 = 1473529742325407185540416487537612465189869383161838138383863033575293817135218553055973325857269118219041602971813973919025686562460789946104526983373925508272707933534592189732683735440805478222783605568274241084963090744480360993656587771778757461612919160894779254758334452854066521288673310419198851991819627662981573667076225459404009857983025927477176966111790347594575351184875653395185719233949213450894170078845932168528522589013379762955294754168074749 e1 = 745699 e2 = 745709 c1 = 23144512980313393199971544624329972186721085732480740903664101556117858633662296801717263237129746648060819811930636439097159566583505473503864453388951643914137969553861677535238877960113785606971825385842502989341317320369632728661117044930921328060672528860828028757389655254527181940980759142590884230818 c2 = 546013011162734662559915184213713993843903501723233626580722400821009012692777901667117697074744918447814864397339744069644165515483680946835825703647523401795417620543127115324648561766122111899196061720746026651004752859257192521244112089034703744265008136670806656381726132870556901919053331051306216646512080226785745719900361548565919274291246327457874683359783654084480603820243148644175296922326518199664119806889995281514238365234514624096689374009704546
main.py
from Crypto.Util.number import * import gmpy2 from flag import flag p = getPrime(512) q = getPrime(512) r = getPrime(512) n1 = p * q n2 = p * q * r e1 = getPrime(20) e2 = int(gmpy2.next_prime(e1)) m = bytes_to_long(flag) c1 = pow(m, e1, n1) c2 = pow(m, e2, n2) print("n1 = {}".format(n1)) print("n2 = {}".format(n2)) print("e1 = {}".format(e1)) print("e2 = {}".format(e2)) print() print("c1 = {}".format(c1)) print("c2 = {}".format(c2))
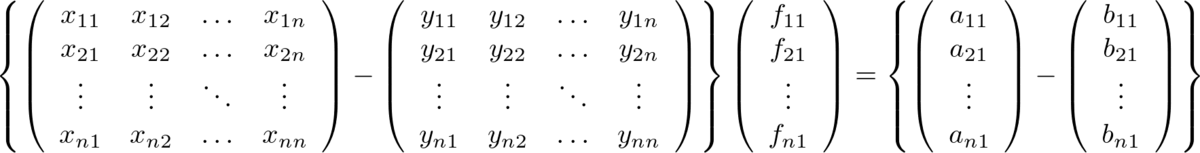
アプローチ:合同式を変形してCommon Modulus Attack
main.pyを読むとが互いに素であり、同一の
を暗号化しているため、
を
上で表現できればCommon Modulus Attackに持ち込めることが分かります。
ここで、は
であるため、
は
上で
と表現できます。
そのため、にそれぞれ
をかけることで、
となるので、
をCommon Modulus Attackによって求めることが可能になります。
以下はソルバになります。
from Crypto.Util.number import * import gmpy2 def decrypt(n1, n2, e1, e2, c1, c2): r = n2 // n1 new_c1 = (c1 * pow(r, e1, n2)) % n2 new_c2 = (c2 * pow(r, e2, n2)) % n2 g, x, y = gmpy2.gcdext(e1,e2) if x < 0: x = abs(x) new_c1_inv = inverse(new_c1, n1) rm = (pow(new_c1_inv, x, n1) * pow(new_c2, y, n1)) % n1 else: y = abs(y) new_c2_inv = inverse(new_c2, n1) rm = (pow(new_c1, x, n1) * pow(new_c2_inv, y, n1)) % n1 return rm, r n1 = 112027309284322736696115076630869358886830492611271994068413296220031576824816689091198353617581184917157891542298780983841631012944437383240190256425846911754031739579394796766027697768621362079507428010157604918397365947923851153697186775709920404789709337797321337456802732146832010787682176518192133746223 n2 = 1473529742325407185540416487537612465189869383161838138383863033575293817135218553055973325857269118219041602971813973919025686562460789946104526983373925508272707933534592189732683735440805478222783605568274241084963090744480360993656587771778757461612919160894779254758334452854066521288673310419198851991819627662981573667076225459404009857983025927477176966111790347594575351184875653395185719233949213450894170078845932168528522589013379762955294754168074749 e1 = 745699 e2 = 745709 c1 = 23144512980313393199971544624329972186721085732480740903664101556117858633662296801717263237129746648060819811930636439097159566583505473503864453388951643914137969553861677535238877960113785606971825385842502989341317320369632728661117044930921328060672528860828028757389655254527181940980759142590884230818 c2 = 546013011162734662559915184213713993843903501723233626580722400821009012692777901667117697074744918447814864397339744069644165515483680946835825703647523401795417620543127115324648561766122111899196061720746026651004752859257192521244112089034703744265008136670806656381726132870556901919053331051306216646512080226785745719900361548565919274291246327457874683359783654084480603820243148644175296922326518199664119806889995281514238365234514624096689374009704546 rm, r = decrypt(n1, n2, e1, e2, c1, c2) print(rm) print(long_to_bytes(rm//r))
1450137700311703879663236107307914645851657803708681805893924798730674006177116062897188857467248320975095348348900554537405990687078193743342999747402279742651073686647363070591701007576551983207170287559
b'KosenCTF{HALDYN_D0M3}'
KosenCTF{HALDYN_D0M3}
bitcrypto [326pts, 17solves]
Yoshiking, the master of bit crypto, has the flag. Ask him for the flag.
nc crypto.kosenctf.com 13003
server.py
from Crypto.Util.number import * from secret import flag def legendre_symbol(x, p): a = pow(x, (p-1) // 2, p) if a == 0: return 0 elif a == 1: return 1 else: return -1 def key_gen(bits): p = getPrime(bits) q = getPrime(bits) n = p * q while True: z = getRandomRange(2, n) a, b = legendre_symbol(z, p), legendre_symbol(z, q) if a == -1 and b == -1: break return (n, z), (p, q) def enc(pubkey, m): n, z = pubkey bits = [int(b) for b in "{:b}".format(m)] c = [] for b in bits: while True: x = getRandomRange(2, n) if GCD(x, n) == 1: break c.append( ((z**b) * (x**2)) % n ) return c def dec(privkey, c): p, q = privkey m = "" for b in c: if legendre_symbol(b, p) == 1 and legendre_symbol(b, q) == 1: m += "0" else: m += "1" return int(m, 2) def main(): pubkey, privkey = key_gen(256) keyword = "yoshiking, give me ur flag" m = input("your query: ") if any([c in keyword for c in m]): print("yoshiking: forbidden!") exit() if len(m) > 8: print("yoshiking: too long!") exit() c = enc(pubkey, bytes_to_long(m.encode())) print("token to order yoshiking: ", c) c = [int(x) for x in input("your token: ")[1:-1].split(",")] if len(c) != len(set(c)): print("yoshiking: invalid!") exit() if any([x < 0 for x in c]): print("yoshiking: wow good unintended-solution!") exit() m = long_to_bytes(dec(privkey, c)) if m == keyword.encode(): print("yoshiking: hi!!!! flag!!!! here!!! wowowowowo~~~~~~") print(flag) else: print(m) print("yoshiking: ...?") if __name__ == '__main__': main()
アプローチ:入力クエリをもとに平方剰余、平方非剰余となるトークンを生成
server.pyを読むと以下のことが分かります。
- 入力トークンが
上で平方剰余であれば0、平方非剰余であれば1といった復号処理を行っている
- 復号してkeywordと一致するトークンを入力すればflagを取得できる
- 入力トークンは重複してはならない
- 入力クエリは8文字以内
- 入力クエリの各ビットごとにトークンを生成している(ビットが0ならば
、ビットが1ならば
)
したがって、トークン化された入力クエリをもとに平方剰余、平方非剰余となる数値を生成し、復号時にkeywordとなるトークン列を送ればいいことが分かります。
平方剰余となるトークンは入力クエリのビット0に対応するトークンを2乗、4乗、8乗…としていけば生成できます。また、平方非剰余となるトークンは入力クエリのビット1に対応するトークンを整数倍すれば雑に生成できます(たまに失敗しますが)。
以下はソルバになります。
from pwn import * from Crypto.Util.number import * r = remote('crypto.kosenctf.com', 13003) m = 'xxxxxxxx' recv = r.recvuntil('your query: ') r.sendline(m.encode()) recv = r.recvline() c = eval(recv.decode().strip().split(': ')[-1]) target = 'yoshiking, give me ur flag' target_bin = bin(bytes_to_long(target.encode()))[2:] base_0 = [] base_1 = [] attack = [] base_0_index = 0 base_1_index = 0 base_0_exp = 1 base_1_coeff = 1 for i,bit in enumerate(bin(bytes_to_long(m.encode()))[2:]): if bit == '1': base_1.append(c[i]) else: base_0.append(c[i]) for x in target_bin: if x == '1': attack.append(base_1[base_1_index] * base_1_coeff) base_1_index += 1 if base_1_index == len(base_1): base_1_index = 0 base_1_coeff += 1 else: attack.append(base_0[base_0_index] ** base_0_exp) base_0_index += 1 if base_0_index == len(base_0): base_0_index = 0 base_0_exp *= 2 recv = r.recvuntil('your token: ') r.sendline(str(attack).encode()) result = r.recvline() print(result.decode()) flag = r.recvline() print(flag.decode())
yoshiking: hi!!!! flag!!!! here!!! wowowowowo~~~~~~
KosenCTF{yoshiking_is_clever_and_wild_god_of_crypt}
KosenCTF{yoshiking_is_clever_and_wild_god_of_crypt}
padding oracle [326pts, 17solves]
As you know, AES-CBC is vulnerable to the oracle attack by padding. Today I resolved the security issue.
nc padding-oracle.kosenctf.com 13004
server.py
from Crypto.Cipher import AES from binascii import hexlify, unhexlify from flag import flag import os import signal def pad(m: bytes) -> bytes: l = 16 - len(m) % 16 return bytes([l]) * l + m def unpad(m: bytes) -> bytes: l = m[0] assert 1 <= l <= 16 assert bytes([l]) * l == m[:l] return m[l:] def main(): key = os.urandom(16) iv = os.urandom(16) aes = AES.new(key=key, mode=AES.MODE_CBC, iv=iv) cipher = aes.encrypt(pad(flag)) print(hexlify(iv + cipher).decode()) signal.alarm(300) while True: c = unhexlify(input()) try: iv, c = c[:16], c[16:] m = AES.new(key=key, mode=AES.MODE_CBC, iv=iv).decrypt(c) u = unpad(m) print(True) except: print(False) if __name__ == '__main__': main()
アプローチ:Padding Oracle Attackのソルバをから改ざんするように修正し、独自Padding方式に対応する
まずPadding Oracle Attackに関しては、下記の記事が理解しやすいかと思います。
この問題で通常のPadding Oracle Attackとの相違点として注目すべき処理は下記です。
def pad(m: bytes) -> bytes: l = 16 - len(m) % 16 return bytes([l]) * l + m
PKCS #7パディングに見えてしまいますが、よく読むとパディングがサフィックスとしてではなく、プレフィックスとして付与されていることに気づくかと思います。
そのため、ptrlibを使うだけでは解けません
通常のPadding Oracle Attackでは、平文を暗号化した暗号文
が
個に分割できる場合、
を改ざんした値である
を求めることによって、
を特定します。
ですが、今回の問題の場合はパディングがプレフィックスとして付与されるので、を改ざんした値である
を求めることによって、
を特定します。
後ろからやるか前からやるかの違いしかありません
以下はソルバになります。
from pwn import * from binascii import hexlify, unhexlify BLOCK_SIZE = 16 r = remote('padding-oracle.kosenctf.com', 13004) def padding_is_valid(x, pad_num, dec, target_cipher): attempt_bytes = bytes([x]) + bytes(BLOCK_SIZE - pad_num) adjust_bytes = b'' for c in dec: adjust_bytes += bytes([c ^ pad_num]) send_code = hexlify(adjust_bytes + attempt_bytes) + target_cipher r.sendline(send_code) result = r.recvline() if b'True' in result: return True else: return False flag = b'' enc = unhexlify(r.recvline().decode().strip()) cipher_blocks = [enc[i:i+BLOCK_SIZE] for i in range(0, len(enc), BLOCK_SIZE)] for i in range(len(cipher_blocks) - 1): prev_cipher = cipher_blocks[i] target_cipher = hexlify(cipher_blocks[i + 1]) x = 0 pad_num = 1 m = b'' dec = b'' while True: if padding_is_valid(x, pad_num, dec, target_cipher): print(f'{bytes([x])}: {bytes([pad_num]) * pad_num}') m += bytes([x ^ pad_num ^ prev_cipher[pad_num - 1]]) dec += bytes([x ^ pad_num]) pad_num += 1 x = 0 if pad_num <= BLOCK_SIZE: continue break x += 1 if x > 0xFF: print('Byte Not Found') break flag += m print(flag) print('-'*50)
b'\xda': b'\x01'
b'$': b'\x02\x02'
b' ': b'\x03\x03\x03'
b'\xce': b'\x04\x04\x04\x04'
b'\x84': b'\x05\x05\x05\x05\x05'
b'\xc5': b'\x06\x06\x06\x06\x06\x06'
b'n': b'\x07\x07\x07\x07\x07\x07\x07'
b'\xa5': b'\x08\x08\x08\x08\x08\x08\x08\x08'
b'\xa4': b'\t\t\t\t\t\t\t\t\t'
b'2': b'\n\n\n\n\n\n\n\n\n\n'
b'g': b'\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b'
b't': b'\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c'
b'\xea': b'\r\r\r\r\r\r\r\r\r\r\r\r\r'
b'\x9e': b'\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e'
b'\x86': b'\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f'
b'\xe4': b'\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10'
b'\x03\x03\x03Turkey in de '
--------------------------------------------------
[snip]
--------------------------------------------------
b'D': b'\x01'
b'\x11': b'\x02\x02'
b'\xc3': b'\x03\x03\x03'
b'J': b'\x04\x04\x04\x04'
b'\xcf': b'\x05\x05\x05\x05\x05'
b'D': b'\x06\x06\x06\x06\x06\x06'
b'\xc1': b'\x07\x07\x07\x07\x07\x07\x07'
b'\xb4': b'\x08\x08\x08\x08\x08\x08\x08\x08'
b'\xff': b'\t\t\t\t\t\t\t\t\t'
b'u': b'\n\n\n\n\n\n\n\n\n\n'
b'\xa9': b'\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b'
b'v': b'\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c\x0c'
b'o': b'\r\r\r\r\r\r\r\r\r\r\r\r\r'
b'r': b'\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e\x0e'
b'\xfe': b'\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f'
b'a': b'\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10\x10'
b'\x03\x03\x03Turkey in de straw, turkey in de hay KosenCTF{0r4c13_5urviv35_57i11_n0w} Turk'
--------------------------------------------------
[snip]
KosenCTF{0r4c13_5urviv35_57i11_n0w}
padrsa [426pts, 7solves]
Textbook-RSA is sometimes weak. I padded it to improve the security.
nc crypto.kosenctf.com 13001
server.py
import os import signal from binascii import unhexlify, hexlify from Crypto.Util.number import * from flag import flag r = os.urandom(8) nonce = 1 p = getPrime(256) q = getPrime(256) n = p * q es = set() def pad(x: bytes) -> bytes: global r, nonce y = long_to_bytes(r[0] | nonce) + x + r nonce += 1 r = long_to_bytes(((bytes_to_long(r) << 1) ^ nonce) & (2**64 - 1)) return y def encrypt(m: bytes, e: int) -> bytes: m_ = bytes_to_long(pad(m)) return long_to_bytes(pow(m_, e, n)) MENU = """ 1. Encrypt the flag 2. Encrypt your message 3. EXIT """ signal.alarm(30) print("n: {}".format(n)) while True: print(MENU) choice = input("> ") if choice not in ["1", "2"]: break e = int(input("e: ")) if not(3 <= e <= 65537): print("[-] invalid e") break if e in es: print("[-] e already used") break if choice == "1": m = flag if choice == "2": m = unhexlify(input("m: ")) c = encrypt(m, e) print("c: {}".format(hexlify(c).decode())) es.add(e)
アプローチ:paddingの不備をついて、Hastad's Broadcast Attack
非想定解法っぽいので、雑に書きます。
この問題で注目すべき処理は下記です。
def pad(x: bytes) -> bytes: global r, nonce y = long_to_bytes(r[0] | nonce) + x + r nonce += 1 r = long_to_bytes(((bytes_to_long(r) << 1) ^ nonce) & (2**64 - 1)) return y
rは64bitの乱数ですが、nonceの初期値が固定のため、64回程度padding(rを64回左シフト)することでrが固定されます。
したがって、同一の平文mを異なるnで暗号化する処理に持ち込めるため、Hastad's Broadcast Attackが可能になります。
以下はnとcを集めるスクリプトです。
from pwn import * ns = [] cs = [] for _ in range(71): nonce = 1 e = 3 r = remote('crypto.kosenctf.com', 13001) n = int(r.recvline().decode().strip().split(' ')[-1]) while e <= 71: print(f'{nonce=}') recv = r.recvuntil('> ') r.sendline(b'1') recv = r.recvuntil('e: ') r.sendline(str(e).encode()) c = int(r.recvline().decode().strip().split(' ')[-1],16) nonce += 1 e += 1 ns.append(n) cs.append(c)
あとは集めたn,cを使ってHastad's Broadcast Attackをするだけです。
KosenCTF{p13as3_mak4_padding_unpr3dictab13}
まとめ
- 良問が多くて楽しめました
- ただ、CTFで土日を潰すと月曜日にも疲れが残って仕事がキツくなることを学びました
- Web, Revも復習したいと思います
- コンテスト中にWrite-up書く癖をつけようと思います
SECCON Beginners CTF 2020 Write-up
はじめに
2020/05/23に ~ 2020/05/24に開催されたSECCON Beginners CTF 2020に会社の同期とチームを結成して参加しました.
チームとしては17問解いて19位でした (1009チーム中).
今回は自分が解いた5問のWrite-upを書きます.


Rev
yakisoba [Easy, 144solved, 156pts]
Would you like to have a yakisoba code?
(Hint: You'd better automate your analysis)
> file yakisoba yakisoba: ELF 64-bit LSB pie executable x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, for GNU/Linux 3.2.0, BuildID[sha1]=fc0031f79ea88d284f3177f980b40110c2612f3e, stripped
アプローチ:シンボリック実行
とりあえずidaでフローグラフをみてみます.

これを読む気にはなりませんね…(1つ1つのロジックは単純だったので気合があれば読めるのかも?)
(Hint: You'd better automate your analysis)
ヒントに従って、angrで自動解析することにします.
idaでmain関数を確認すると,0x000006D2に到達できればいいことがわかります.

そのため,ソルバは以下のようになります.
import angr p = angr.Project('./yakisoba', load_options={'auto_load_libs': False}) state = p.factory.entry_state() sim = p.factory.simulation_manager(state) sim.explore(find=(0x400000 + 0x6d2,), avoid=(0x400000 + 0x6f7,)) print(sim.found[0].posix.dumps(0))
> python solve.py
WARNING | 2020-05-25 06:15:25,139 | cle.loader | The main binary is a position-independent executable. It is being loaded with a base address of 0x400000.
b'ctf4b{sp4gh3tt1_r1pp3r1n0}\x00\xd9\xd9\xd9\xd9'
ctf4b{sp4gh3tt1_r1pp3r1n0}
ghost [Medium, 68solved, 279pts]
A program written by a ghost 👻
chall.gs
/flag 64 string def /output 8 string def (%stdin) (r) file flag readline not { (I/O Error\n) print quit } if 0 1 2 index length { 1 index 1 add 3 index 3 index get xor mul 1 463 { 1 index mul 64711 mod } repeat exch pop dup output cvs print ( ) print 128 mod 1 add exch 1 add exch } repeat (\n) print quit
output.txt
3417 61039 39615 14756 10315 49836 44840 20086 18149 31454 35718 44949 4715 22725 62312 18726 47196 54518 2667 44346 55284 5240 32181 61722 6447 38218 6033 32270 51128 6112 22332 60338 14994 44529 25059 61829 52094
アプローチ:動的解析
問題名やスクリプトの文法(スタック指向)からghostscript (postscript?)だということがわかります.
最初はドキュメントを読みながら愚直に解析していたのですが,途中で出力結果が入力文字列の長さに依存しないことに気づきました.
> gs chall.gs ctf4b 3417 61039 39615 14756 10315
そのため,方針を静的解析ではなく,indexごとに文字空間を全探索する動的解析に切り替えました.
ソルバは以下のようになります.
import subprocess import string enc_flag = ['3417', '61039', '39615', '14756', '10315', '49836', '44840', '20086', '18149', '31454', '35718', '44949', '4715', '22725', '62312', '18726', '47196', '54518', '2667', '44346', '55284', '5240', '32181', '61722', '6447', '38218', '6033', '32270', '51128', '6112', '22332', '60338', '14994', '44529', '25059', '61829', '52094'] flag = b'ctf4b{' while len(flag) < len(enc_flag): for c in string.printable: p = subprocess.Popen(['gs', 'chall.gs'], stdin=subprocess.PIPE, stdout=subprocess.PIPE, stderr=subprocess.PIPE) p.stdin.write(flag + c.encode() + b'\n') p.stdin.flush() res = p.stdout.readlines()[-1].decode().strip().split()[-1] if res == enc_flag[len(flag)]: print(f'flag is {flag.decode() + c}') flag += c.encode() break
> python solve.py
flag is ctf4b{s
flag is ctf4b{st
flag is ctf4b{st4
flag is ctf4b{st4c
flag is ctf4b{st4ck
flag is ctf4b{st4ck_
flag is ctf4b{st4ck_m
flag is ctf4b{st4ck_m4
flag is ctf4b{st4ck_m4c
flag is ctf4b{st4ck_m4ch
flag is ctf4b{st4ck_m4ch1
flag is ctf4b{st4ck_m4ch1n
flag is ctf4b{st4ck_m4ch1n3
flag is ctf4b{st4ck_m4ch1n3_
flag is ctf4b{st4ck_m4ch1n3_1
flag is ctf4b{st4ck_m4ch1n3_1s
flag is ctf4b{st4ck_m4ch1n3_1s_
flag is ctf4b{st4ck_m4ch1n3_1s_4
flag is ctf4b{st4ck_m4ch1n3_1s_4_
flag is ctf4b{st4ck_m4ch1n3_1s_4_l
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_f
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_fu
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_fun
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_fun!
flag is ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_fun!}
ctf4b{st4ck_m4ch1n3_1s_4_l0t_0f_fun!}
siblangs [Medium, 37solved, 363pts]
Well, they look so similar... siblangs.apk
> file siblangs.apk siblangs.apk: Zip archive data, at least v?[0] to extract

とりあえずsiblangs.apkをunzipします.
ここでctf4bでgrepすると以下のようなJavaScriptで書かれた処理を見つけることができます.
> grep -r 'ctf4b' ./siblangs
./siblangs/assets/index.android.bundle:
[snipped]
state={flagVal:"ctf4b{",xored:[34,63,3,77,36,20,24,8,25,71,110,81,64,87,30,33,81,15,39,90,17,27]},t.handleFlagChange=function(o){t.setState({flagVal:o})},t.onPressValidateFirstHalf=function(){if("ios"===h.Platform.OS){for(var o="AKeyFor"+h.Platform.OS+"10.3",l=t.state.flagVal,n=0;n<t.state.xored.length;n++)if(t.state.xored[n]!==parseInt(l.charCodeAt(n)^o.charCodeAt(n%o.length),10))return void h.Alert.alert("Validation A Failed","Try again...");h.Alert.alert("Validation A Succeeded","Great! Have you checked the other one?")}else h.Alert.alert("Sorry!","Run this app on iOS to validate! Or you can try the other one :)")},t.onPressValidateLastHalf=function(){"android"===h.Platform.OS?p.default.validate(t.state.flagVal,function(t){t?h.Alert.alert("Validation B Succeeded","Great! Have you checked the other one?"):h.Alert.alert("Validation B Failed","Learn once, write anywhere ... anywhere?")}):h.Alert.alert("Sorry!","Run this app on Android to validate! Or you can try the other one :)")},t}return(0,n.default)
[snipped]
ここでは,key (AkeyForios10.3)と入力文字列のxorが[34,63,3,77,36,20,24,8,25,71,110,81,64,87,30,33,81,15,39,90,17,27]と一致するかのチェックを行っています.
そのため,以下の処理でflagを復元できます.
a = [34,63,3,77,36,20,24,8,25,71,110,81,64,87,30,33,81,15,39,90,17,27] key = b"AKeyForios10.3"*2 flag = bytearray() for x,k in zip(a,key): flag.append(x^k) print(flag.decode())
ctf4b{jav4_and_j4va5cr
どうやら残りのflagを取得するにはh.Platform.OS?p.default.validateを調べる必要があるようです.
dex2jarを用いてclasses.dexをclasses-dex2jar.jarに変換し,JD-GUIでJava側のソースコードを確認するとValidateFlagModule.classでValidateを行っていることが確認できます.
ValidateFlagModule.classでは,encrypted flagをAES-GCMで復号し,入力文字列と比較する処理を行っています.
また,このクラスでは,復号の際にハードコーディングされたsecret keyを利用しているので,encrypted flagをdecryptする処理は以下のように簡単に再現することができます.
import java.security.SecureRandom; import javax.crypto.Cipher; import javax.crypto.SecretKey; import javax.crypto.spec.GCMParameterSpec; import javax.crypto.spec.SecretKeySpec; class DecryptLastFlag { private static final int GCM_IV_LENGTH = 12; private static final SecretKey secretKey = new SecretKeySpec("IncrediblySecure".getBytes(), 0, 16, "AES"); private final SecureRandom secureRandom = new SecureRandom(); public static void main(String[] args) { byte[] arrayOfByte = new byte[43]; byte[] tmp8_6 = arrayOfByte; tmp8_6[0] = 95; byte[] tmp13_8 = tmp8_6; tmp13_8[1] = -59; byte[] tmp18_13 = tmp13_8; tmp18_13[2] = -20; byte[] tmp23_18 = tmp18_13; tmp23_18[3] = -93; byte[] tmp28_23 = tmp23_18; tmp28_23[4] = -70; byte[] tmp33_28 = tmp28_23; tmp33_28[5] = 0; byte[] tmp38_33 = tmp33_28; tmp38_33[6] = -32; byte[] tmp44_38 = tmp38_33; tmp44_38[7] = -93; byte[] tmp50_44 = tmp44_38; tmp50_44[8] = -23; byte[] tmp56_50 = tmp50_44; tmp56_50[9] = 63; byte[] tmp62_56 = tmp56_50; tmp62_56[10] = -9; byte[] tmp68_62 = tmp62_56; tmp68_62[11] = 60; byte[] tmp74_68 = tmp68_62; tmp74_68[12] = 86; byte[] tmp80_74 = tmp74_68; tmp80_74[13] = 123; byte[] tmp86_80 = tmp80_74; tmp86_80[14] = -61; byte[] tmp92_86 = tmp86_80; tmp92_86[15] = -8; byte[] tmp98_92 = tmp92_86; tmp98_92[16] = 17; byte[] tmp104_98 = tmp98_92; tmp104_98[17] = -113; byte[] tmp110_104 = tmp104_98; tmp110_104[18] = -106; byte[] tmp116_110 = tmp110_104; tmp116_110[19] = 28; byte[] tmp122_116 = tmp116_110; tmp122_116[20] = 99; byte[] tmp128_122 = tmp122_116; tmp128_122[21] = -72; byte[] tmp134_128 = tmp128_122; tmp134_128[22] = -3; byte[] tmp140_134 = tmp134_128; tmp140_134[23] = 1; byte[] tmp146_140 = tmp140_134; tmp146_140[24] = -41; byte[] tmp152_146 = tmp146_140; tmp152_146[25] = -123; byte[] tmp158_152 = tmp152_146; tmp158_152[26] = 17; byte[] tmp164_158 = tmp158_152; tmp164_158[27] = 93; byte[] tmp170_164 = tmp164_158; tmp170_164[28] = -36; byte[] tmp176_170 = tmp170_164; tmp176_170[29] = 45; byte[] tmp182_176 = tmp176_170; tmp182_176[30] = 18; byte[] tmp188_182 = tmp182_176; tmp188_182[31] = 71; byte[] tmp194_188 = tmp188_182; tmp194_188[32] = 61; byte[] tmp200_194 = tmp194_188; tmp200_194[33] = 70; byte[] tmp206_200 = tmp200_194; tmp206_200[34] = -117; byte[] tmp212_206 = tmp206_200; tmp212_206[35] = -55; byte[] tmp218_212 = tmp212_206; tmp218_212[36] = 107; byte[] tmp224_218 = tmp218_212; tmp224_218[37] = -75; byte[] tmp230_224 = tmp224_218; tmp230_224[38] = -89; byte[] tmp236_230 = tmp230_224; tmp236_230[39] = 3; byte[] tmp242_236 = tmp236_230; tmp242_236[40] = 94; byte[] tmp248_242 = tmp242_236; tmp248_242[41] = -71; byte[] tmp254_248 = tmp248_242; tmp254_248[42] = 30; Cipher localCipher = Cipher.getInstance("AES/GCM/NoPadding"); GCMParameterSpec localGCMParameterSpec = new GCMParameterSpec(128, arrayOfByte, 0, 12); localCipher.init(2, secretKey, localGCMParameterSpec); arrayOfByte = localCipher.doFinal(arrayOfByte, 12, arrayOfByte.length - 12); for (byte x : arrayOfByte) { System.out.print((char)x); } System.out.println(); } }
1pt_3verywhere}
最後に2つのflagを合わせることで完全なflagを得ることができます.
ctf4b{jav4_and_j4va5cr1pt_3verywhere}
Crypto
Noisy equations [Easy, 76solved, 261pts]
noise hides flag.
nc noisy-equations.quals.beginners.seccon.jp 3000
problem.py
from os import getenv from time import time from random import getrandbits, seed FLAG = getenv("FLAG").encode() SEED = getenv("SEED").encode() L = 256 N = len(FLAG) def dot(A, B): assert len(A) == len(B) return sum([a * b for a, b in zip(A, B)]) coeffs = [[getrandbits(L) for _ in range(N)] for _ in range(N)] seed(SEED) answers = [dot(coeff, FLAG) + getrandbits(L) for coeff in coeffs] print(coeffs) print(answers)
アプローチ:差をとることでノイズを消去する
problem.pyを読むと44変数(これはncすれば分かります)の連立方程式の解がflagになっていることが分かります.
ですが,この連立方程式はノイズが加わったanswersを与えられるため,そのままでは解くことができません.
しかし,ありがたいことにノイズはSEDDで固定されるため,coeffsとanswersを2回取得し,差をとることでノイズを消去することができます.


あとは連立方程式を解くだけです.
SymPyやNumPyで逆行列を求めようとしたら微妙に上手くいかなかったので
ソルバは以下のようになります.
from random import getrandbits, seed from pwn import * import numpy as np r = remote('noisy-equations.quals.beginners.seccon.jp', 3000) coeffs_a = eval(r.recvline().decode().strip()) answers_a = eval(r.recvline().decode().strip()) r = remote('noisy-equations.quals.beginners.seccon.jp', 3000) coeffs_b = eval(r.recvline().decode().strip()) answers_b = eval(r.recvline().decode().strip()) coeffs = [[a - b for a,b in zip(coeff_a, coeff_b)] for coeff_a, coeff_b in zip(coeffs_a,coeffs_b)] answers = [a - b for a, b in zip(answers_a,answers_b)] coeffs_mat = np.array(coeffs) answers_mat = np.array(answers) for i in range(len(coeffs_mat)-1): for j in range(i+1, len(coeffs_mat)): coef = coeffs_mat[j][i] / coeffs_mat[i][i] coeffs_mat[j] -= coeffs_mat[i] * coef answers_mat[j] -= answers_mat[i] * coef for i in range(len(coeffs_mat)-1, 0, -1): answers_mat[i] /= coeffs_mat[i][i] coeffs_mat[i] /= coeffs_mat[i][i] for j in range(i): answers_mat[j] -= answers_mat[i] * coeffs_mat[j][i] coeffs_mat[j][i] = 0 print(answers_mat) flag = '' for x in answers_mat[1:]: flag += chr(round(x)) print('c' + flag)
> python solve.py
[1.4373191156143338e+78 116.00000000002152 102.00000000002716
51.99999999999115 97.99999999999812 122.99999999991692 114.00000000001545
52.00000000002947 110.00000000002872 99.99999999992944 48.00000000004317
109.00000000003224 94.99999999995093 52.99999999994877 50.999999999970356
51.00000000005113 100.00000000006227 95.00000000002443 49.00000000000767
53.00000000000038 95.00000000005183 110.00000000002365 50.99999999993853
99.00000000000699 51.000000000033324 53.000000000014914
53.000000000011006 51.99999999985527 114.00000000002838
120.99999999998803 95.00000000000075 102.00000000002628 47.99999999999231
114.0000000000347 95.00000000002042 53.00000000003555 50.99999999998389
98.99999999995198 116.99999999995693 113.99999999994883 48.99999999994941
54.999999999976076 121.00000000008183 125.00000000002167]
ctf4b{r4nd0m_533d_15_n3c3554ry_f0r_53cur17y}
1文字目は誤差ってたので無視しました
ctf4b{r4nd0m_533d_15_n3c3554ry_f0r_53cur17y}
RSA Calc [Medium, 52solved, 319pts]
F(1337)=FLAG!
nc rsacalc.quals.beginners.seccon.jp 10001
server.py
from Crypto.Util.number import * from params import p, q, flag import binascii import sys import signal N = p * q e = 65537 d = inverse(e, (p-1)*(q-1)) def input(prompt=''): sys.stdout.write(prompt) sys.stdout.flush() return sys.stdin.buffer.readline().strip() def menu(): sys.stdout.write('''---------- 1) Sign 2) Exec 3) Exit ''') try: sys.stdout.write('> ') sys.stdout.flush() return int(sys.stdin.readline().strip()) except: return 3 def cmd_sign(): data = input('data> ') if len(data) > 256: sys.stdout.write('Too long\n') return if b'F' in data or b'1337' in data: sys.stdout.write('Error\n') return signature = pow(bytes_to_long(data), d, N) sys.stdout.write('Signature: {}\n'.format(binascii.hexlify(long_to_bytes(signature)).decode())) def cmd_exec(): data = input('data> ') signature = int(input('signature> '), 16) if signature < 0 or signature >= N: sys.stdout.write('Invalid signature\n') return check = long_to_bytes(pow(signature, e, N)) if data != check: sys.stdout.write('Invalid signature\n') return chunks = data.split(b',') stack = [] for c in chunks: if c == b'+': stack.append(stack.pop() + stack.pop()) elif c == b'-': stack.append(stack.pop() - stack.pop()) elif c == b'*': stack.append(stack.pop() * stack.pop()) elif c == b'/': stack.append(stack.pop() / stack.pop()) elif c == b'F': val = stack.pop() if val == 1337: sys.stdout.write(flag + '\n') else: stack.append(int(c)) sys.stdout.write('Answer: {}\n'.format(int(stack.pop()))) def main(): sys.stdout.write('N: {}\n'.format(N)) while True: try: command = menu() if command == 1: cmd_sign() if command == 2: cmd_exec() elif command == 3: break except: sys.stdout.write('Error\n') break if __name__ == '__main__': signal.alarm(60) main()
アプローチ:署名を合成する
server.pyを読むと計算結果が1337になる関数Fの署名を得ることができればflagも取得できることが分かります.
しかし,署名を行うには次の制約があるようです.
- 署名対象に
Fが含まれていてはならない - 署名対象に
1337が含まれていてはならない
次に計算部分のロジックを確認すると1336,1,+,Fであれば計算結果が1337になることが分かります.
あとは署名を行うだけなのですが,1336,1,+,Fは署名の制約を受けるため直接署名を行うことができません(1336,1,+,FにはFが含まれているため).
ここで,となることを利用し,この制約を回避します.
具体的には1336,1,+,Fを232340431793906185350214として素因数分解し,Fまたは1337が含まれないトークンを2つ生成し,
これらのトークンに対して署名を行い,合成することで1336,1,+,Fの署名を入手します.
ソルバは以下のようになります.
from pwn import * from Crypto.Util.number import * TOKEN = b'1336,1,+,F' t1 = 12530004045462689 t2 = 2 * 181**2 * 283 r = remote('rsacalc.quals.beginners.seccon.jp', 10001) received = r.recvline() N = int(received.decode().strip().split(' ')[1],10) received = r.recvuntil('> ') r.sendline(b'1') r.sendline(long_to_bytes(t1)) received = r.recvline() t1_sign = int(received.decode().strip().split(' ')[2],16) received = r.recvuntil('> ') r.sendline(b'1') r.sendline(long_to_bytes(t2)) received = r.recvline() t2_sign = int(received.decode().strip().split(' ')[2],16) token_sign = t1_sign * t2_sign % N received = r.recvuntil('> ') r.sendline(b'2') r.sendline(TOKEN) r.sendline(hex(token_sign)[2:]) received = r.recvline() print(received.decode())
python solve.py
data> signature> ctf4b{SIgn_n33ds_P4d&H4sh}
ctf4b{SIgn_n33ds_P4d&H4sh}

因みに3rd bloodでした(ちょっと嬉しかった)
まとめ
UTCTF 2020 Write-up
はじめに
2020/03/07 ~ 2020/03/09に開催されたUTCTFにチーム(NekochanNano!)で参加しました.
成績
チームとしては23問解いて44位でした (1001チーム中).
今回は自分が解いた12問のWrite-upを書きます.
Rev
[basics] Reverse Engineering
know there's a string in this binary somewhere.... Now where did I leave it?
> file calc calc: ELF 64-bit LSB shared object x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=f5ca6bb761ab5d70a7ecd74041af001fe88ea383, for GNU/Linux 3.2.0, not stripped
アプローチ:strings
> strings calc | grep utflag
utflag{str1ngs_1s_y0ur_fr13nd}
utflag{str1ngs_1s_y0ur_fr13nd}
.PNG2
In an effort to get rid of all of the bloat in the .png format, I'm proud to announce .PNG2! The first pixel is #7F7F7F, can you get the rest of the image?
> file pic.png2 pic.png2: data
> xxd pic.png2 | head 00000000: 504e 4732 7769 6474 683d 05cf 6865 6967 PNG2width=..heig 00000010: 6874 3d02 887f 7f7f 7f7f 7f7f 7f7f 7f7f ht=............. 00000020: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000030: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000040: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000050: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000060: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000070: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000080: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................ 00000090: 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f 7f7f ................
アプローチ:formatのエスパー
xxdの結果からwidth=0x05cf, height=0x0288であることが確認できます.
また,最初のPixelが#7F7F7Fであることから22byte以降はPixel値で構成されていると考えることができます.
これらの情報をもとにPNGを復元すると次のようになります.

utflag{j139adfo_93u12hfaj}
以下は復元に利用したコードです.
from PIL import Image from Crypto.Util.number import * # width=0x05cf, height=0x0288 with open('pic.png2', 'rb') as f: data = f.read() header = data[:21] pixels = data[21:] flag_img = Image.new('RGB', (0x05cf, 0x0288)) x = 0 y = 0 for i in range(0, len(pixels)-3, 3): rgb = pixels[i:i+3] flag_img.putpixel((x,y), (rgb[0],rgb[1],rgb[2])) x += 1 if x == 0x05cf: x = 0 y += 1 flag_img.save('./flag.png')
Forensics
Observe Closely
A simple image with a couple of twists...
アプローチ:foremost
.pngなのでzstegを利用してhidden dataを抽出します.
> zsteg Griffith_Observatory.png
[?] 2763 bytes of extra data after image end (IEND), offset = 0x1f30f
extradata:0 .. file: Zip archive data, at least v2.0 to extract
00000000: 50 4b 03 04 14 00 00 00 08 00 45 81 5b 50 b3 10 |PK........E.[P..|
00000010: f1 08 1b 0a 00 00 18 41 00 00 0d 00 1c 00 68 69 |.......A......hi|
00000020: 64 64 65 6e 5f 62 69 6e 61 72 79 55 54 09 00 03 |dden_binaryUT...|
00000030: 42 3e 58 5e 46 3e 58 5e 75 78 0b 00 01 04 e8 03 |B>X^F>X^ux......|
00000040: 00 00 04 e8 03 00 00 ed 5b 7d 6c 14 c7 15 9f bb |........[}l.....|
00000050: f3 99 e3 c3 e7 03 ec e0 00 89 8f 06 24 d3 d4 c7 |............$...|
00000060: f9 6c 8c dd c8 e0 b3 7d f6 ba 3a 03 21 76 4a d5 |.l.....}..:.!vJ.|
00000070: c0 76 7d 7b e7 5b 71 1f d6 dd 5e 6b d3 56 a1 72 |.v}{.[q...^k.V.r|
00000080: 42 73 22 4e 50 3f a4 a6 52 55 fe 44 55 a5 80 2a |Bs"NP?..RU.DU..*|
00000090: 21 2b 6a 25 23 23 92 a8 51 0a 7f b4 a5 45 55 dd |!+j%##..Q....EU.|
000000a0: 28 1f 26 4a 13 87 86 c8 4d 03 db 99 dd 79 7b 3b |(.&J....M....y{;|
000000b0: 73 77 85 b4 aa aa 4a fb 93 f6 de ce 6f de 7b f3 |sw....J.....o.{.|
000000c0: 76 76 76 3d eb 99 f7 64 24 3a e8 74 38 10 c0 85 |vvv=...d$:.t8...|
000000d0: f6 22 52 3a e8 33 ca bd 94 bf d6 6d aa 60 ae 0b |."R:.3.....m.`..|
000000e0: ad c5 bf 0f a0 ad a8 16 97 6b 2c 7a bc 4c 3a 59 |.........k,z.L:Y|
000000f0: e9 31 db 31 ec ce 52 9e 97 5b 11 2b 1d 16 59 83 |.1.1..R..[.+..Y.|
b1,rgb,lsb,xy .. text: "This is one of the twists: there is no flag here!"
b2,r,msb,xy .. text: "PUUDADTP"
b2,bgr,lsb,xy .. text: "*sj 51\t}Z"
b3,g,msb,xy .. text: "@C$\tS\"LR"
b3,rgb,lsb,xy .. text: "@`0B-0R("
b4,r,msb,xy .. text: "11a 6pFdPWP"
b4,g,msb,xy .. text: "R@W5pc&7DU3GF\"`sF"
b4,b,msb,xy .. text: "ud&!qcFu"
b4,rgb,msb,xy .. text: "#pFEp&`c"
b4,bgr,msb,xy .. text: "' Cv@%vc"
zipが埋め込まれていることが分かったので,foremostを利用してzipを抽出します.
> foremost Griffith_Observatory.png foremost: /usr/local/etc/foremost.conf: No such file or directory Processing: Griffith_Observatory.png |foundat=hidden_binaryUT *|
圧縮されていたhidden_binaryを実行すればflagを取得できます.
> ./hidden_binary
Ah, you found me!
utflag{2fbe9adc2ad89c71da48cabe90a121c0}
utflag{2fbe9adc2ad89c71da48cabe90a121c0}
Spectre
I found this audio file, but I don't think it's any song I've ever heard... Maybe there's something else inside?
> file song.wav song.wav: RIFF (little-endian) data, WAVE audio, Microsoft PCM, 16 bit, mono 44100 Hz
アプローチ:Spectrogramの確認
Sonic VisualiserでSpectrogramを確認するとflagを確認できます.
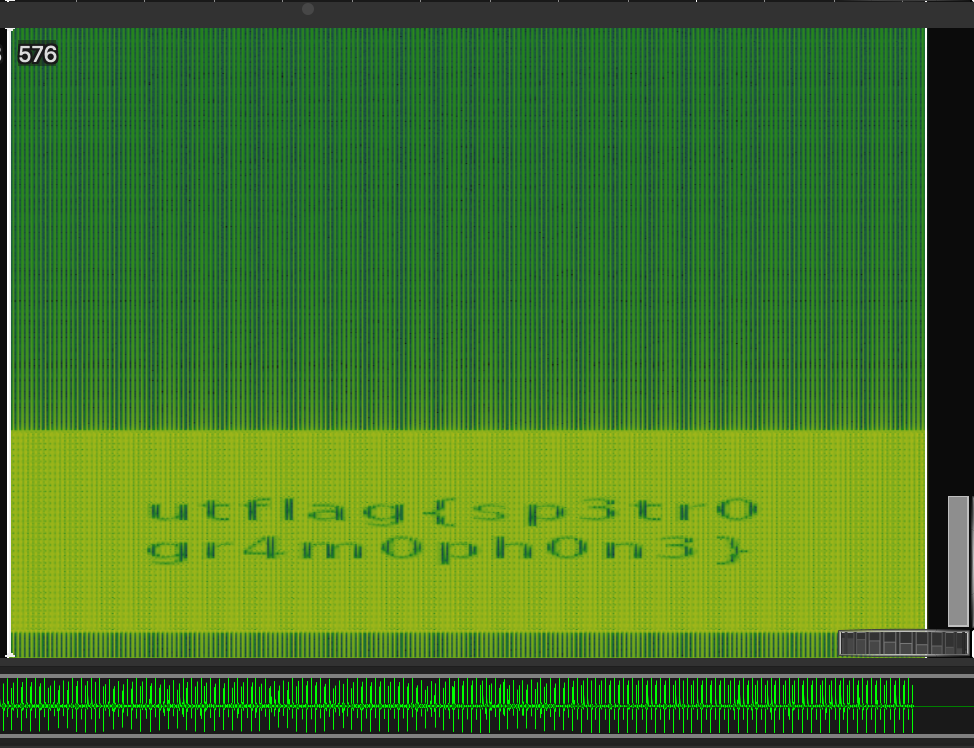
utflag{sp3tr0gr4m0ph0n3}
The Legend of Hackerman, Pt. 1
My friend Hackerman tried to send me a secret transmission, but I think some of it got messed up in transit. Can you fix it?
> file hackerman.png hackerman.png: data
アプローチ:headerの書き換え
xxdすると.pngファイルシグネチャの上位4byteが0x00で上書きされていることが分かるので,バイナリエディタなどを利用してheaderを8950 4e47に書き換えることでflagを取得できます.
> xxd hackerman.png | head 00000000: 0000 0000 0d0a 1a0a 0000 000d 4948 4452 ............IHDR 00000010: 0000 04a8 0000 029e 0806 0000 0081 2e23 ...............# 00000020: af00 0028 257a 5458 7452 6177 2070 726f ...(%zTXtRaw pro 00000030: 6669 6c65 2074 7970 6520 6578 6966 0000 file type exif.. 00000040: 78da ad9c 6992 1c37 9285 ffe3 1473 04ec x...i..7.....s.. 00000050: cb71 e058 cce6 067d fcf9 1e32 4991 92ba .q.X...}...2I... 00000060: a7db ac45 1349 5565 4520 e0ee 6f71 78c8 ...E.IUeE ..oqx. 00000070: 9d7f fcef 75ff c33f 2394 ec72 69bd 8e5a ....u..?#..ri..Z 00000080: 3dff e491 479c fca5 fbcf 3fe3 fd1e 7c7e =...G.....?...|~ 00000090: bfbf 7f66 7fff a5ff feed eb6e 1c1f dfdf ...f.......n....

utflag{3lit3_h4ck3r}
The Legend of Hackerman, Pt. 2
Ok, I've received another file from Hackerman, but it's just a Word Document? He said that he attached a picture of the flag, but I can't find it...
> file Hacker.docx Hacker.docx: Microsoft Word 2007+
アプローチ:unzip
画像ファイルを探しやすくするために.docxをunzipします.
unzip Hacker.docx -d Hacher Archive: Hacker.docx inflating: Hacher/_rels/.rels inflating: Hacher/word/fontTable.xml inflating: Hacher/word/styles.xml inflating: Hacher/word/_rels/document.xml.rels inflating: Hacher/word/settings.xml inflating: Hacher/word/media/image97.png inflating: Hacher/word/media/image102.png [snip] inflating: Hacher/word/media/image25.png inflating: Hacher/word/media/image24.png inflating: Hacher/word/media/image169.jpeg inflating: Hacher/word/media/image37.png inflating: Hacher/word/numbering.xml inflating: Hacher/docProps/core.xml inflating: Hacher/docProps/app.xml inflating: Hacher/[Content_Types].xml inflating: Hacher/word/document.xml
Hacher/word/media内の.pngを確認するとflagを見つけることができます.

utflag{unz1p_3v3ryth1ng}
Crypto
[basics] crypto
Can you make it through all of the encodings?
binary.txt
01010101 01101000 00101101 01101111 01101000 00101100 00100000 01101100 01101111 01101111 01101011 01110011 00100000 01101100 01101001 01101011 01100101 00100000 01110111 01100101 00100000 01101000 01100001 01110110 01100101 00100000 01100001 01101110 01101111 01110100 01101000 01100101 01110010 00100000 01100010 01101100 01101111 01100011 01101011 00100000 01101111 01100110 00100000 01110100 01100101 01111000 01110100 00101100 00100000 01110111 01101001 01110100 01101000 00100000 01110011 01101111 01101101 01100101 00100000 01110011 01101111 01110010 01110100 00100000 01101111 01100110 00100000 01110011 01110000 01100101 01100011 01101001 01100001 01101100 00100000 01100101 01101110 01100011 01101111 01100100 01101001 01101110 01100111 00101110 00100000 01000011 01100001 01101110 00100000 01111001 01101111 01110101 00100000 01100110 01101001 01100111 01110101 01110010 01100101 00100000 01101111 01110101 01110100 00100000 01110111 01101000 01100001 01110100 00100000 01110100 01101000 01101001 01110011 00100000 01100101 01101110 01100011 01101111 01100100 01101001 01101110 01100111 00100000 01101001 01110011 00111111 00100000 00101000 01101000 01101001 01101110 01110100 00111010 00100000 01101001 01100110 00100000 01111001 01101111 01110101 00100000 01101100 01101111 01101111 01101011 00100000 01100011 01100001 01110010 01100101 01100110 01110101 01101100 01101100 01111001 00101100 00100000 01111001 01101111 01110101 00100111 01101100 01101100 00100000 01101110 01101111 01110100 01101001 01100011 01100101 00100000 01110100 01101000 01100001 01110100 00100000 01110100 01101000 01100101 01110010 01100101 00100000 01101111 01101110 01101100 01111001 00100000 01100011 01101000 01100001 01110010 01100001 01100011 01110100 01100101 01110010 01110011 00100000 01110000 01110010 01100101 01110011 01100101 01101110 01110100 00100000 01100001 01110010 01100101 00100000 01000001 00101101 01011010 00101100 00100000 01100001 00101101 01111010 00101100 00100000 00110000 00101101 00111001 00101100 00100000 01100001 01101110 01100100 00100000 01110011 01101111 01101101 01100101 01110100 01101001 01101101 01100101 01110011 00100000 00101111 00100000 01100001 01101110 01100100 00100000 00101011 00101110 00100000 01010011 01100101 01100101 00100000 01101001 01100110 00100000 01111001 01101111 01110101 00100000 01100011 01100001 01101110 00100000 01100110 01101001 01101110 01100100 00100000 01100001 01101110 00100000 01100101 01101110 01100011 01101111 01100100 01101001 01101110 01100111 00100000 01110100 01101000 01100001 01110100 00100000 01101100 01101111 01101111 01101011 01110011 00100000 01101100 01101001 01101011 01100101 00100000 01110100 01101000 01101001 01110011 00100000 01101111 01101110 01100101 00101110 00101001 00001010 01010100 01101101 01010110 00110011 01001001 01000111 01001110 01101111 01011001 01010111 01111000 01110011 01011010 01010111 00110101 01101110 01011010 01010011 01000101 01100111 01010001 00110010 01000110 01110101 01001001 01001000 01101100 01110110 01100100 01010011 01000010 01101101 01100001 01010111 01100100 00110001 01100011 01101101 01010101 01100111 01100010 00110011 01010110 00110000 01001001 01001000 01100100 01101111 01011001 01011000 01010001 01101110 01100011 01111001 01000010 01101110 01100010 00110010 01101100 01110101 01011010 01111001 01000010 01110110 01100010 01101001 01000010 01101111 01011010 01011000 01001010 01101100 01010000 01111001 01000010 01001010 01100100 01000011 01000010 01110011 01100010 00110010 00111001 01110010 01100011 01111001 01000010 01110011 01100001 01010111 01110100 01101100 01001001 01001000 01010010 01101111 01011010 01010011 01000010 01110011 01011010 01011000 01010010 00110000 01011010 01011000 01001010 01111010 01001001 01000111 01000110 01111001 01011010 01010011 01000010 01111010 01100001 01000111 01101100 01101101 01100100 01000111 01010110 01101011 01001001 01000111 01001010 00110101 01001001 01001000 01001110 01110110 01100010 01010111 01010101 01100111 01011001 00110010 00111001 01110101 01100011 00110011 01010010 01101000 01100010 01101110 01010001 01110101 01001001 01000011 01101000 01101111 01100001 01010111 00110101 00110000 01001111 01101001 01000010 00110101 01100010 00110011 01010101 01100111 01100010 01010111 01101100 01101110 01100001 01001000 01010001 01100111 01100100 00110010 01000110 01110101 01100100 01000011 01000010 00110000 01100010 01111001 01000010 01111010 01100100 01000111 01000110 01111001 01100100 01000011 01000010 01110011 01100010 00110010 00111001 01110010 01100001 01010111 00110101 01101110 01001001 01001000 01010110 01110111 01001001 01000110 01001010 01110110 01100010 01010111 01000110 01110101 01001001 01001000 01000010 01101100 01100010 00110011 01000010 01110011 01011010 01010011 01101011 01110101 01000011 01101101 01110100 00110010 01011001 01101110 01001110 01111000 01100011 01101101 01010001 01110011 01001001 01000111 01101100 00110101 01011010 01010011 01100100 01101001 01100010 01111001 01000010 01110010 01100100 01101110 01100100 00110101 01011001 00110010 01010001 01100111 01011010 01001000 01001010 01110110 01011001 01101101 00111000 01101000 01001001 01000110 01101000 00110101 01011010 01111001 01000010 01110111 01100101 01010111 01001001 01100111 01011010 01001000 01001010 01110110 01001001 01001000 01000010 01111010 01100101 01000111 01110100 00110010 01001001 01000011 01101000 01110010 01100101 01000111 00110100 01100111 01100100 00110010 01110100 01110000 01100010 01000111 00111000 01100111 01011010 01001000 01001010 01110110 01001001 01001000 01001010 01110010 01011001 01101101 00110101 01110110 01011001 00110010 01010001 01110101 01001100 01101001 00110100 01110000 01001001 01001000 01110000 01110010 01011001 01101101 01010001 00110110 01001001 01000111 01110011 01100111 01011001 00110010 01010110 01110011 01011001 00110010 01010010 01111010 01011010 01000111 01010110 01101011 01100011 00110011 01101100 00110100 01001001 01000111 00110001 01111010 01100101 01101110 01001010 01110110 01011001 01101001 00110100 01100111 01010101 00110011 01100111 01100111 01011010 01001000 01001010 01110110 01001001 01001000 01000010 00110101 01100100 01101110 01011010 00110101 01011010 00110011 01001110 00110100 01100011 01010011 01000010 01101011 01100010 00110010 01101000 01101011 01001100 01000011 01000010 01010100 01001010 00110010 01011010 01110110 01001001 01000111 01010010 01110010 01100100 01010111 00111001 00110100 01001001 01001000 01100100 01110000 01001001 01001000 01100100 01110110 01011001 00110010 01001110 01110010 01100011 01010111 00111000 01100111 01100001 00110011 01101000 01110101 01001001 01000111 01001010 01110110 01100101 01101110 01011010 01110010 01100010 01010111 00111001 01110101 01001001 01000111 00111001 01101101 01100010 00110010 01001010 01110000 01001001 01000111 01110100 00110010 01100101 01101110 01001010 01110010 01100010 01000111 00111001 01101011 01100011 00110010 00110000 01100111 01100010 01011000 01001010 01110010 01011001 01101101 01110100 01110100 01011010 01000111 00111001 01101001 01001001 01000111 01100100 01111010 01011010 01001000 01001001 01100111 01100001 01111001 01000010 01110100 01100101 01010111 01001010 01101001 01100010 00110010 01001110 00110110 01100101 01011000 01101000 01110101 01100010 00110011 01101000 01110100 01100010 01111001 01000010 01101011 01100101 01010011 01000010 01110010 01001001 01000111 00110101 01111010 01100011 01001000 01000010 01110110 01011001 01101101 00111001 00110100 01011010 01000011 01000010 01110100 01100011 01101101 01110100 01101001 01100001 00110010 00110001 01101011 01100010 00110010 01001001 01100111 01001100 01010011 01000010 00110001 01100101 01001000 01101100 01101110 01100101 01000011 01000010 01110010 01011001 01111001 01000010 01110010 01001001 01000111 01001110 01101100 01100010 01000111 01001110 01101011 01100011 00110010 01010010 01101100 01011010 01001000 01001110 00110101 01100101 01000011 01000010 01110100 01100011 00110011 01110000 01111001 01100010 00110010 01001001 01110101 01001001 01000101 00110001 01110010 01100101 01000011 01000010 01110000 01100101 01010111 01010101 01100111 01100011 01001000 01001110 00110100 01100010 01101001 01000010 01101011 01100011 01101101 00111000 01100111 01100011 01001000 01001110 00110100 01100001 00110011 01011001 01100111 01100011 01001000 01011010 01110010 01100011 01010100 00111000 01100111 01100011 01101110 01001110 00110100 01011010 01000100 01101111 01100111 01010010 00110010 00111000 01100111 01100100 01011000 01101000 00110101 01011010 01111001 01000010 01101011 01100011 01101101 01110100 01101011 01001001 01000111 01010010 01111001 01100010 01111001 01000010 01110111 01100100 01101101 01110100 01111000 01001001 01001000 01001110 01101010 01001001 01001000 01000110 00110101 01100011 00110011 01101000 01111000 01001001 01000111 01010010 00110101 01001001 01000111 01111000 01110110 01001001 01001000 01101100 01110111 01001001 01000111 01010010 01111001 01100010 01111001 01000010 01110111 01100101 01010111 01001010 00110011 01100001 00110010 01010001 01100111 01011010 01010111 01010010 01110111 01100100 01101101 01110100 01111000 01100101 01111001 00110100 01110101 01001100 01101110 00110000 01100111 01001100 01010011 01000010 01101110 01100011 01101110 01001110 01110100 01100011 01101001 01000010 00110011 01100010 00110010 01110100 00110100 01011001 01111001 01000010 01101011 01100011 01101101 01110100 01101011 01001001 01001000 01001110 01110111 01001001 01000111 01101100 00110101 01011010 01010011 01000010 01101010 01100010 00110010 00111000 01100111 01011010 01001000 01001010 01110010 01011010 01000011 01000010 00110110 01100001 00110010 01010010 01101011 01100010 00110010 01001010 00110100 01001100 01000011 01000010 01110000 01100101 01010111 01010101 01100111 01100100 01011000 01101000 00110101 01011010 01111001 01000010 01101110 01100011 01101101 01110100 01101011 01001001 01000111 01010010 01111001 01100010 01111001 01000010 01110100 01100101 01010111 01001010 01101001 01100010 00110010 01001110 00110110 01100101 01011000 01101000 01110101 01100010 00110011 01101000 01110100 01100010 00110010 01001101 01100111 01100011 01001000 01101100 01101001 01001001 01000111 01010101 01110011 01001001 01000111 01010001 01110011 01001001 01001000 01000001 01110011 01001001 01001000 01011001 01100111 01100001 01111001 01110111 01100111 01100001 00110011 01101000 01110101 01001001 01001000 01000101 01100111 01100001 00110010 01001010 01110110 01001100 01101001 01000010 01001010 01100101 01010111 01010101 01100111 01100010 01010111 01110100 00110100 01001001 01001000 01110000 01101001 01100101 01010111 01111000 01110010 01100010 01001000 01011010 01110000 01001001 01000111 01100100 00110101 01011001 01101110 01010101 01100111 01100101 01010111 01010110 01101011 01001001 01000111 01010010 01111001 01100010 01111001 01000010 01101001 01100010 00110011 01100100 01110010 01100011 00110011 01101000 01111010 01100101 01001000 01000101 01100111 01100010 01011000 01001010 01110010 01011001 01101101 01110100 01110100 01011010 01000111 00111001 01101001 01011001 01111001 01000010 01110011 01100001 01010011 01000010 01101001 01100010 00110011 01110000 00110010 01100001 00110010 00110001 01111010 01100101 01001000 01000101 01100111 01011010 01001000 01001010 01110110 01100100 01111001 01000010 01110010 01100101 01000111 00110100 01100111 01100011 00110011 01101000 01110111 01100010 00110010 01001010 01101001 01100011 00110011 01101000 01111000 01001001 01000111 00110001 00110101 01100100 00110011 01100100 00110101 01100101 01000011 01000010 01101110 01100101 01010111 01001010 01110101 01011001 01111001 01000010 01111010 01100101 01000011 01000010 01101011 01100011 01101101 00111000 01100111 01010100 00110011 01101000 01111000 01100100 01101110 01001110 01101010 01100011 01101001 01000010 00110010 01100001 00110011 01101000 01111000 01011010 01010111 01110100 01111000 01100010 01111001 00110100 01100111 01010011 00110011 01101000 00110101 01011010 01001000 01001010 01110110 01011001 01101001 01000010 01111000 01011001 01101101 00111001 01110010 01011010 01000011 01000010 00110011 01100010 00110010 01010010 01111001 01100101 01010111 00110100 01100111 01100011 00110010 01001101 01100111 01011010 01001000 01101011 01100111 01011010 01010111 01001110 01110110 01001001 01001000 01000010 01101001 01100010 00110010 01000110 01101100 01100010 00110011 01101000 01110100 01100001 01010011 01000010 01110010 01100101 01000111 01110100 00110010 01100001 01010111 01001110 01111010 01011001 01111010 01101111 01100111 01011010 00110010 00111000 01100111 01100100 01011000 01101000 00110101 01011010 01111001 01000010 01101011 01100011 01101101 01110100 01101011 01001001 01000011 01100100 01110110 01001010 01111001 01000010 01101010 01100011 01101110 01101100 01101110 01011001 01111001 01000010 01101100 01100101 01101001 01000010 00110011 01100101 01010111 01001110 01101011 01001001 01001000 01101100 01110111 01011010 01000111 00111001 00110100 01001001 01001000 01001110 00110100 01001001 01000111 01010010 01111001 01100010 01111001 01000010 01110010 01100100 01101110 01110000 01111001 01100001 00110010 01111000 01110110 01011010 01000011 01110111 01100111 01011001 00110011 01101011 01100111 01011010 01001000 01001010 01110010 01011010 01000011 01100100 01101010 01001001 01001000 01110000 01101001 01100101 01010111 01111000 01110010 01100010 01001000 01011010 01110000 01001001 01000111 01010010 01111001 01100010 01111001 01000010 00110011 01100101 01010111 01001110 01101011 01001001 01000111 00110001 00110101 01100100 00110011 01100100 00110101 01100101 01000011 01000010 01110100 01100011 01101101 01110100 01101001 01100001 00110010 00110001 01101011 01100010 00110010 01001001 01100111 01100011 00110011 01100111 01100111 01011010 01001000 01001010 01110110 01001001 01000111 01010010 01110110 01100001 01000111 01010001 01110011 01001001 01001000 01000010 00110101 01100100 01101110 01011010 00110101 01011010 00110010 00111001 01110101 01001001 01000111 01111000 01110000 01001001 01000011 01100100 01101011 01001010 01111001 01110111 01100111 01100001 00110011 01101000 01110101 01001001 01000111 01001110 00110101 01001001 01001000 01101100 00110100 01001100 01101001 01000010 01011010 01100101 01000111 00110001 01110110 01001001 01000111 01101100 00110101 01011010 01010011 01000010 00110001 01100101 01001000 01101100 01101110 01001001 01000111 01110011 01100111 01100011 01000111 00111001 01101110 01001001 01000111 00110001 01111001 01100001 00110010 01001010 01110010 01100010 01010111 01010010 01110110 01011001 01101101 01001101 01110011 01001001 01000111 01101100 00110101 01011010 01010011 01000010 01110100 01100001 00110011 01100111 01100111 01100011 00110011 01101000 01110111 01100010 00110010 01001001 01100111 01011010 01001000 01001010 01110110 01001001 01000111 01001010 01110110 01011001 00110010 01010001 01100111 01100101 01011000 01000001 01100111 01011010 01001000 01001010 01110110 01001001 01000111 01100100 00110101 01011001 01101101 00110101 01101010 01001001 01000111 01111000 01110010 01011001 00110010 00111001 01110101 01001001 01001000 01101100 00110100 01001001 01000111 00110001 00110101 01100100 00110011 01100100 00110101 01100101 01000011 01000010 01101110 01100101 01010111 01001010 01110101 01011001 01111001 01000010 01101011 01100011 01101101 01110100 01101011 01001001 01000111 01001110 01111001 01100101 01010111 01100011 01100111 01011010 01011000 01101111 01100111 01100011 00110011 01100111 01100111 01011010 01001000 01001010 01110110 01001001 01000101 00111001 00110100 01100011 01011000 01011010 01111010 01011001 00110011 01001001 01100111 01100100 01101101 01110100 00110100 01100011 01010111 01010110 01110010 01100011 01010111 00111000 01110101 01000011 01101110 01001010 01101110 01100001 01000111 00110101 00110100 01100011 00110010 01010010 01101101 01100101 01011000 01001110 01101011 01100100 01000111 01100100 01101111 01100100 01010011 01000101 01100111 01100011 01010111 01100100 01101101 01001001 01000111 01101100 01111010 01011001 01010111 01110011 01100111 01011001 00110011 01010010 01101111 01100100 01001000 01010110 01110000 01100001 00110010 01010101 01100111 01011010 01000111 01101100 01110010 01001001 01001000 01110000 01110010 01100010 01101110 01010010 01101111 01100001 01000111 01110100 00110100 01001001 01001000 01001010 00110100 01100011 01010111 01111000 01101011 01011010 00110010 00110101 00110100 01100011 00110010 01111000 01110000 01100011 01010011 01000010 01111001 01100001 01011000 01001110 00110101 01100101 01010111 01110100 01101111 01100010 01101101 01110011 01110101 01001001 01000111 01101100 01110010 01100101 01000111 01110011 01100111 01100100 01001000 01010101 01100111 01100011 01111001 01000010 01101010 01100101 01011000 01001110 01110101 01001001 01000111 01001110 01101110 01100101 01000011 01000010 01111010 01100101 01011000 01101011 01100111 01100011 01010111 01100100 01101101 01100101 01000011 01000010 01110000 01100011 00110011 01101000 01101100 01001001 01000111 01110100 01101010 01011001 00110010 01100100 00110100 01011010 01001000 01010101 00110110 01001001 01000111 01011010 01101011 01011001 00110011 01101100 01111010 01100010 01101110 01110100 01101111 01001101 01001000 01011010 01100110 01011010 01000111 01101011 00110000 01011010 01001000 01010110 01100110 01100100 01101101 01101011 00110000 01011010 01000110 00111001 00110000 01011000 00110011 01001001 00110000 01100101 01011000 01101100 01100110 01100011 01101110 01101000 01111000 01100010 01000111 01010001 01110111 01100110 01010011 00110100 01100111 01100011 01010111 01100100 01101101 01001001 01001000 01011010 00110000 01100101 01011000 01101011 01100111 01011001 00110011 01010010 01101111 01011010 01010011 01000010 01101011 01100001 01011000 01001110 01101011 01001001 01001000 01001101 01100111 01100101 01010111 01100100 01101011 01001001 01000111 01100100 01101010 01001001 01001000 01001010 00110100 01100011 01010111 01111000 01101011 01011010 00110010 00110101 00110100 01100011 00110010 01111000 01110000 01100011 01010011 01000010 00110000 01100100 01010011 01000010 01110111 01011010 01101110 01010110 01101011 01001001 01001000 01110000 01101101 01100100 01001000 01101100 01101100 01100100 01000111 01101000 01110101 01001001 01000111 01100100 01101010 01011001 01111001 01000010 01101011 01100001 01011000 01010010 00110001 01001001 01001000 01010110 01101110 01100101 01000111 01010001 01100111 01011010 00110010 01001101 01100111 01100101 01101110 01001110 00110001 01100100 01001000 01001001 01100111 01011001 01101101 01101000 01101110 01100100 01101110 01101100 01110010 01011010 01010111 00110101 01110010 01001100 01000011 01000010 01111010 01100001 01000111 01010101 01100111 01100100 01000111 01010001 01100111 01100101 01000111 01110100 01111010 01100101 01011000 01101100 01111000 01001001 01001000 01010010 00110001 01001001 01000111 01101000 01101110 01011010 01000011 01000010 00110001 01011010 01111001 01000010 00110110 01100011 00110010 01010101 01100111 01100011 00110010 01001110 01101011 01100001 00110011 01100111 01100111 01100011 00110011 01101100 00110101 01001100 01101001 01000010 01110000 01011010 00110010 01111000 01110010 01001001 01001000 01000110 01101110 01011010 01101001 01000010 01110010 01100001 01001000 01000010 01101110 01100011 01010111 01110100 01101100 01001001 01000111 01010010 01110000 01100001 01111001 01000010 01111001 01100001 01011000 01001110 00110101 01100101 01010111 01110100 01101111 01100010 01101101 01110011 01101000
アプローチ:binary -> base64 -> rot16 -> substitution cipher
CyberChefを使って変換していきます.
From Binary
Uh-oh, looks like we have another block of text, with some sort of special encoding. Can you figure out what this encoding is? (hint: if you look carefully, you'll notice that there only characters present are A-Z, a-z, 0-9, and sometimes / and +. See if you can find an encoding that looks like this one.) TmV3IGNoYWxsZW5nZSEgQ2FuIHlvdSBmaWd1cmUgb3V0IHdoYXQncyBnb2luZyBvbiBoZXJlPyBJdCBsb29rcyBsaWtlIHRoZSBsZXR0ZXJzIGFyZSBzaGlmdGVkIGJ5IHNvbWUgY29uc3RhbnQuIChoaW50OiB5b3UgbWlnaHQgd2FudCB0byBzdGFydCBsb29raW5nIHVwIFJvbWFuIHBlb3BsZSkuCmt2YnNxcmQsIGl5ZSdibyBrdnd5Y2QgZHJvYm8hIFh5ZyBweWIgZHJvIHBzeGt2IChreG4gd2tpbG8gZHJvIHJrYm5vY2QuLi4pIHprYmQ6IGsgY2VsY2RzZGVkc3l4IG1zenJvYi4gU3ggZHJvIHB5dnZ5Z3N4cSBkb2hkLCBTJ2ZvIGRrdW94IHdpIHdvY2NrcW8ga3huIGJvenZrbW9uIG9mb2JpIGt2enJrbG9kc20gbXJrYmttZG9iIGdzZHIgayBteWJib2N6eXhub3htbyBkeSBrIG5zcHBvYm94ZCBtcmtia21kb2IgLSB1eHlneCBrYyBrIGNlbGNkc2RlZHN5eCBtc3pyb2IuIE1reCBpeWUgcHN4biBkcm8gcHN4a3YgcHZrcT8gcnN4ZDogR28gdXh5ZyBkcmtkIGRybyBwdmtxIHNjIHF5c3hxIGR5IGxvIHlwIGRybyBweWJ3a2QgZWRwdmtxey4uLn0gLSBncnNtciB3b2t4YyBkcmtkIHNwIGl5ZSBjb28gZHJrZCB6a2Rkb2J4LCBpeWUgdXh5ZyBncmtkIGRybyBteWJib2N6eXhub3htb2MgcHliIGUsIGQsIHAsIHYgaywga3huIHEga2JvLiBJeWUgbWt4IHpieWxrbHZpIGd5YnUgeWVkIGRybyBib3drc3hzeHEgbXJrYmttZG9iYyBsaSBib3p2a21zeHEgZHJvdyBreG4gc3hwb2Jic3hxIG15d3d5eCBneWJuYyBzeCBkcm8gT3hxdnNjciB2a3hxZWtxby4gS3h5ZHJvYiBxYm9rZCB3b2RyeW4gc2MgZHkgZWNvIHBib2Flb3htaSBreGt2aWNzYzogZ28gdXh5ZyBkcmtkICdvJyBjcnlnYyBleiB3eWNkIHlwZG94IHN4IGRybyBrdnpya2xvZCwgY3kgZHJrZCdjIHpieWxrbHZpIGRybyB3eWNkIG15d3d5eCBtcmtia21kb2Igc3ggZHJvIGRvaGQsIHB5dnZ5Z29uIGxpICdkJywga3huIGN5IHl4LiBZeG1vIGl5ZSB1eHlnIGsgcG9nIG1ya2JrbWRvYmMsIGl5ZSBta3ggc3hwb2IgZHJvIGJvY2QgeXAgZHJvIGd5Ym5jIGxrY29uIHl4IG15d3d5eCBneWJuYyBkcmtkIGNyeWcgZXogc3ggZHJvIE94cXZzY3Igdmt4cWVrcW8uCnJnaG54c2RmeXNkdGdodSEgcWdmIGlzYWsgY3RodHVpa2UgZGlrIHprbnRoaGt4IHJ4cWxkZ254c2xpcSByaXN5eWtobmsuIGlreGsgdHUgcyBjeXNuIGNneCBzeXkgcWdmeCBpc3hlIGtjY2d4ZHU6IGZkY3lzbntoMHZfZGk0ZHVfdmk0ZF90X3I0eXlfcnhxbGQwfS4gcWdmIHZ0eXkgY3RoZSBkaXNkIHMgeWdkIGdjIHJ4cWxkZ254c2xpcSB0dSBwZnVkIHpmdHlldGhuIGdjYyBkaXR1IHVneGQgZ2MgenN1dHIgYmhndnlrZW5rLCBzaGUgdGQgeGtzeXlxIHR1IGhnZCB1ZyB6c2Ugc2Nka3ggc3l5LiBpZ2xrIHFnZiBraHBncWtlIGRpayByaXN5eWtobmsh
From Base64
New challenge! Can you figure out what's going on here? It looks like the letters are shifted by some constant. (hint: you might want to start looking up Roman people).
kvbsqrd, iye'bo kvwycd drobo! Xyg pyb dro psxkv (kxn wkilo dro rkbnocd...) zkbd: k celcdsdedsyx mszrob. Sx dro pyvvygsxq dohd, S'fo dkuox wi wocckqo kxn bozvkmon ofobi kvzrklodsm mrkbkmdob gsdr k mybboczyxnoxmo dy k nsppoboxd mrkbkmdob - uxygx kc k celcdsdedsyx mszrob. Mkx iye psxn dro psxkv pvkq? rsxd: Go uxyg drkd dro pvkq sc qysxq dy lo yp dro pybwkd edpvkq{...} - grsmr wokxc drkd sp iye coo drkd zkddobx, iye uxyg grkd dro mybboczyxnoxmoc pyb e, d, p, v k, kxn q kbo. Iye mkx zbylklvi gybu yed dro bowksxsxq mrkbkmdobc li bozvkmsxq drow kxn sxpobbsxq mywwyx gybnc sx dro Oxqvscr vkxqekqo. Kxydrob qbokd wodryn sc dy eco pboaeoxmi kxkvicsc: go uxyg drkd 'o' crygc ez wycd ypdox sx dro kvzrklod, cy drkd'c zbylklvi dro wycd mywwyx mrkbkmdob sx dro dohd, pyvvygon li 'd', kxn cy yx. Yxmo iye uxyg k pog mrkbkmdobc, iye mkx sxpob dro bocd yp dro gybnc lkcon yx mywwyx gybnc drkd cryg ez sx dro Oxqvscr vkxqekqo.
rghnxsdfysdtghu! qgf isak cthtuike dik zknthhkx rxqldgnxsliq risyykhnk. ikxk tu s cysn cgx syy qgfx isxe kccgxdu: fdcysn{h0v_di4du_vi4d_t_r4yy_rxqld0}. qgf vtyy cthe disd s ygd gc rxqldgnxsliq tu pfud zftyethn gcc ditu ugxd gc zsutr bhgvykenk, she td xksyyq tu hgd ug zse scdkx syy. iglk qgf khpgqke dik risyykhnk!
ROT16
alright, you're almost there! Now for the final (and maybe the hardest...) part: a substitution cipher. In the following text, I've taken my message and replaced every alphabetic character with a correspondence to a different character - known as a substitution cipher. Can you find the final flag? hint: We know that the flag is going to be of the format utflag{...} - which means that if you see that pattern, you know what the correspondences for u, t, f, l a, and g are. You can probably work out the remaining characters by replacing them and inferring common words in the English language. Another great method is to use frequency analysis: we know that 'e' shows up most often in the alphabet, so that's probably the most common character in the text, followed by 't', and so on. Once you know a few characters, you can infer the rest of the words based on common words that show up in the English language.
hwxdnitvoitjwxk! gwv yiqa sjxjkyau tya padjxxan hngbtwdnibyg hyiooaxda. yana jk i soid swn ioo gwvn yinu asswntk: vtsoid{x0l_ty4tk_ly4t_j_h4oo_hngbt0}. gwv ljoo sjxu tyit i owt ws hngbtwdnibyg jk fvkt pvjoujxd wss tyjk kwnt ws pikjh rxwloauda, ixu jt naioog jk xwt kw piu istan ioo. ywba gwv axfwgau tya hyiooaxda!
換字式暗号はquipqiupでサクッと解きます.
congratulations! you have finished the beginner cryptography challenge. here is a flag for all your hard efforts: utflag{n0w_th4ts_wh4t_i_c4ll_crypt0}. you will find that a lot of cryptography is just building off this sort of basic knowledge, and it really is not so bad after all. hope you enjoyed the challenge!
utflag{n0w_th4ts_wh4t_i_c4ll_crypt0}
One True Problem
Two of my friends were arguing about which CTF category is the best, but they encrypted it because they didn't want anyone to see. Lucky for us, they reused the same key; can you recover it?
Here are the ciphertexts:
213c234c2322282057730b32492e720b35732b2124553d354c22352224237f1826283d7b0651
3b3b463829225b3632630b542623767f39674431343b353435412223243b7f162028397a103e
アプローチ:ciphertext同士のXOR
問題名と問題文からOne Time Padでの使いまわしをしたときに生じる問題を問われていることが分かります.
同一のを用いて,
One Time Padでを暗号化すると次のようになります.
そのため,同士のXORが
となることを利用し,を復元することで,
求めることができます.
に関してですが,問題文でカテゴリについて議論しているとあるので,カテゴリと
のXORをとることで
の一部を復元することができます.
以下のコードを用いてカテゴリとのXORをとると
CRYPTOGRAPHYとBINARY EXPLOITATIONがに含まれていることが分かります.
from Crypto.Util.number import * c1 = 0x213c234c2322282057730b32492e720b35732b2124553d354c22352224237f1826283d7b0651 c2 = 0x3b3b463829225b3632630b542623767f39674431343b353435412223243b7f162028397a103e categorys = [b'CRYPTOGRAPHY', b'BINARY EXPLOITATION', b'REVERSE ENGINEERING', b'NETWORKING', b'WEB', b'FORENSICS', b'MISC'] xor_msg = long_to_bytes(c1 ^ c2) for category in categorys: print('-'* 30) print(category) for i in range(len(xor_msg) - len(category) + 1): msg = bytearray() for c,m in zip(category, xor_msg[i:]): msg.append(c ^ m) print(msg)
------------------------------ b'CRYPTOGRAPHY' [snip] bytearray(b'B+:GUO_ROVH]') bytearray(b':1NQTWG\\GPLX') bytearray(b' EXPLOITATIO') ------------------------------ b'BINARY EXPLOITATION' [snip] bytearray(b'V&^Q<Q!<;GMOQTORIKO') bytearray(b'-Y^/ZXY&OQLWIZGTMNX') bytearray(b'RY IS CRYPTOGRAPHY!') [snip]
EXPLOITATIO, RY IS CRYPTOGRAPHY!をもとに手作業で確定文字列を増やしていくことでを全文復元することができます.
THE BEST CTFONE IS BINARY EXPLOITATION NO THE BEST CATEGORY IS CRYPTOGRAPHY!
あとはを求めるだけです.
msg = b'NO THE BEST CATEGORY IS CRYPTOGRAPHY!' c1 = long_to_bytes(c1) flag = bytearray() for c, m in zip(c1, msg): flag.append(c ^ m) print(flag)
bytearray(b'os\x03\x18kg\x08b\x12 _\x12im3_p4ds}utflag{tw0_tim3_p')
utflag{tw0_tim3_p4ds}
Random ECB
nc crypto.utctf.live 9003
server.py
from Crypto.Cipher import AES from Crypto.Util.Padding import pad from Crypto.Random import get_random_bytes from Crypto.Random.random import getrandbits from secret import flag KEY = get_random_bytes(16) def aes_ecb_encrypt(plaintext, key): cipher = AES.new(key, AES.MODE_ECB) return cipher.encrypt(plaintext) def encryption_oracle(plaintext): b = getrandbits(1) plaintext = pad((b'A' * b) + plaintext + flag, 16) return aes_ecb_encrypt(plaintext, KEY).hex() if __name__ == '__main__': while True: print("Input a string to encrypt (input 'q' to quit):") user_input = input() if user_input == 'q': break output = encryption_oracle(user_input.encode()) print("Here is your encrypted string, have a nice day :)") print(output)
> nc crypto.utctf.live 9003 Input a string to encrypt (input 'q' to quit): 1 Here is your encrypted string, have a nice day :) 0810a77dd0c57f828820ef102fc7269378b7a3b1f807537d5bb3f29cf3206aed Input a string to encrypt (input 'q' to quit): 1 Here is your encrypted string, have a nice day :) 8fe2fded61cef1f605e890b7eaabc8d082c21c2c5d3b89fbda9c556f8ea1d767a14f439f7202eac2d4a5bff21a8f7ed3 Input a string to encrypt (input 'q' to quit): 1 Here is your encrypted string, have a nice day :) 8fe2fded61cef1f605e890b7eaabc8d082c21c2c5d3b89fbda9c556f8ea1d767a14f439f7202eac2d4a5bff21a8f7ed3 Input a string to encrypt (input 'q' to quit): 1 Here is your encrypted string, have a nice day :) 8fe2fded61cef1f605e890b7eaabc8d082c21c2c5d3b89fbda9c556f8ea1d767a14f439f7202eac2d4a5bff21a8f7ed3 Input a string to encrypt (input 'q' to quit): 1 Here is your encrypted string, have a nice day :) 0810a77dd0c57f828820ef102fc7269378b7a3b1f807537d5bb3f29cf3206aed
アプローチ:選択平文攻撃
AES-ECBに対する典型的な選択平文攻撃が可能ですが,
encryption_oracleで入力文字列に50%の確率でAがprefixとして追加されるので,期待通りのplaintextを暗号化できているか何度か確認する必要があります.
以下のソルバではencrypt結果の一致判定を5回行って,prefixによって生じる問題を回避しています (5回しか一致判定をしていないので3.125%の確率でflag1byte分の情報を見逃してしまいます).
また,17byte以降のflagはencrypt結果の17~32byteと49~64byteの一致判定及び1~16byteと33~48byteの一致判定を行うことで復元可能です.
自動化が面倒だったので手動で1文字ずつflagを確定させていきました
import string from socket import * sock = socket(AF_INET, SOCK_STREAM) sock.connect(('crypto.utctf.live', 9003)) confirmed_flag = b'utflag{3cb_w17h_' #16byte flag = b'r4nd0m_pr3f1x' rec = sock.recv(1024).decode('utf-8') for c in '_}' + string.digits + string.ascii_lowercase: print(c) found = False for i in range(5): # msg = b'A' * (15 - len(flag)) + flag + c.encode() # msg += b'A' * (15 - len(flag)) + b'\n' msg = b'A' * (15 - len(flag)) + confirmed_flag[:len(flag)+1] msg += confirmed_flag[len(flag)+1:] + flag + c.encode() msg += b'A' * (15 - len(flag)) + b'\n' sock.send(msg) enc = sock.recv(1024).decode('utf-8').split('\n')[1] # print(enc) if enc[32:64] == enc[96:128] and enc[0:32] == enc[64:96] and len(enc) != 0: print('found') print(c) found = True break if found: print(confirmed_flag.decode() + flag.decode() + c) break
utflag{3cb_w17h_r4nd0m_pr3f1x}
Hill
I found these characters on top of a hill covered with algae ... bruh I can't figure it out can you help me?
wznqca{d4uqop0fk_q1nwofDbzg_eu}
アプローチ:行列サイズのエスパー
出題者はencrypt.pyを配布して
問題名からHill Cipherを用いてflagを暗号化したと推測できます.
ここで行列サイズを2行2列,を26と仮定し,暗号化に用いた行列を
とします.

このとき,flag format からHill Cipherによる暗号化は次のようになっていると考えることができます.

したがって,を求めることで,flagを得ることができます.
は次のようになります.

以下,ソルバです.
import binascii import numpy as np from Crypto.Util.number import inverse def transform_matrix(text): mats = [] for i in range(0, len(text), 4): mats.append([ [text[i] - ord('a'), text[i + 1] - ord('a')], [text[i + 2] - ord('a'), text[i + 3] - ord('a') ], ]) return mats def decrypt(inv_key_mat, mats): flag = '' for mat in mats: # flag_mat = np.round(np.dot(inv_key_mat, mat)) % 26 flag_mat = np.round(np.dot(mat, inv_key_mat)) % 26 print(flag_mat) for row in flag_mat: for x in row: flag += chr(int(x) + ord('a')) print(flag) # enc = b'wznqca{d4uqop0fk_q1nwofDbzg_eu}' enc = b'wznqcaduqopfkqnwofdbzgeu' enc_mat = transform_matrix(enc) target_mat = [[20, 19],[ 5, 11]] inv_target_mat = np.round(np.linalg.inv(target_mat) * np.linalg.det(target_mat)) inv_target = inverse(round(np.linalg.det(inv_target_mat)), 26) inv_target_mat = inv_target_mat * inv_target % 26 key_mat = np.round(np.dot(inv_target_mat, enc_mat[0])) inv_key_mat = np.round(np.linalg.inv(key_mat) * np.linalg.det(key_mat)) inv_key = inverse(round(np.linalg.det(inv_key_mat)), 26) inv_key_mat = np.round(inv_key_mat * inv_key) % 26 decrypt(inv_key_mat, enc_mat)
> python solve.py [[20. 19.] [ 5. 11.]] [[ 0. 6.] [ 3. 13.]] [[ 6. 4.] [17. 20.]] [[18. 2.] [15. 7.]] [[ 4. 17.] [19. 4.]] [[23. 19.] [16. 16.]] utflagdngeruscphertextqq
utflag{d4nger0us_c1pherText_qq}
preタグ使わないと行列書けないはてなmarkdownくん…
preタグ使ったあとにシンタックスハイライト使うとpreタグ内の数式崩壊するの何故?
結局TeXclipで数式を画像化しちゃった
Galois
nc crypto.utctf.live 9004
server.py
import sys from Crypto.Cipher import AES from Crypto.Random import get_random_bytes from secret import flag KEY = get_random_bytes(16) NONCE = get_random_bytes(16) def aes_gcm_encrypt(plaintext): cipher = AES.new(KEY, AES.MODE_GCM, nonce=NONCE) ciphertext, tag = cipher.encrypt_and_digest(plaintext) return ciphertext.hex(), tag.hex() def aes_gcm_decrypt(ciphertext, tag): cipher = AES.new(KEY, AES.MODE_GCM, nonce=NONCE) plaintext = cipher.decrypt_and_verify(ciphertext, tag) return plaintext if __name__ == '__main__': options = '''Welcome to the AES GCM encryption and decryption tool! 1. Encrypt message 2. Decrypt message 3. Quit ''' def encrypt_msg(): print("Input a string to encrypt (must be at least 32 characters):") user_input = input() if len(user_input) < 32: sys.exit() output = aes_gcm_encrypt(user_input.encode()) print("Here is your encrypted string & tag, have a nice day :)") print(output) def decrypt_msg(): print("Input a hex string and its tag to decrypt:") user_input = bytearray.fromhex(input()) tag = bytearray.fromhex(input()) try: output = aes_gcm_decrypt(user_input, tag) except ValueError: print("Decryption failed :(") return print("Here is your decrypted string, have a nice day :)") print(output) def quit(): sys.exit() menu = { '1' : encrypt_msg, '2' : decrypt_msg, '3' : quit } i = 0 print('flag', aes_gcm_encrypt(flag)[0]) while i < 10: print(options) print('Select option: ') choice = input() if choice not in menu.keys(): print("Not a valid choice...") sys.exit() menu[choice]() i += 1
> nc crypto.utctf.live 9004
flag ecdf4c528049b4eec2099b0644ad67075253cfaeb3e4efb4200c5b37393ef99e
Welcome to the AES GCM encryption and decryption tool!
1. Encrypt message
2. Decrypt message
3. Quit
Select option:
1
Input a string to encrypt (must be at least 32 characters):
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
Here is your encrypted string & tag, have a nice day :)
('d8ea6b7fa06f8e99e0258521359e44777776bd81ad9199c2552e71294f488fa2', '623748220dc33b03577ab40ce0edd737')
Welcome to the AES GCM encryption and decryption tool!
1. Encrypt message
2. Decrypt message
3. Quit
Select option:
3
アプローチ:AES-GCMにおける同一KEY及び同一NONCEを用いたEncryptの脆弱性
AES-GCM,初めて知った
AES-GCMについて調べるとAES-GCMは暗号化としてCTRモードを利用し,認証としてGaloisモードを組み合わせたモードであることが分かりました(それはそうでしょ).
つまり,AES-GCMにおける同一KEY及び同一NONCEを用いたEncryptによる問題はAES-CTRを利用した場合でも発生します.
AES-CTRで同一KEY及び同一NONCEを用いたEncrypt行った場合,以下のような問題が発生します.
したがって,以下のソルバでflagを求めることができます.
from Crypto.Util.number import * enc_flag = long_to_bytes(0xecdf4c528049b4eec2099b0644ad67075253cfaeb3e4efb4200c5b37393ef99e) enc_msg = long_to_bytes(0xd8ea6b7fa06f8e99e0258521359e44777776bd81ad9199c2552e71294f488fa2) msg = b'AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA' msg_xor_flag = [m ^ f for m,f in zip(enc_msg, enc_flag)] flag = [chr(m ^ mxf) for m,mxf in zip(msg,msg_xor_flag)] print(''.join(flag))
> python solve.py
utflag{6cm_f0rb1dd3n_4774ck_777}
utflag{6cm_f0rb1dd3n_4774ck_777}
以下のページが参考になりました.
Curveball
My friend Shamir was trying to share the flag with me and some of the other problem writers, but he wanted to make sure it didn't get intercepted in transmission, so he split it up. He said that the secrets that he shared will help us find the flag, but I can't figure it out! These are the secrets I've gathered so far:
(C81E728D9D4C2F636F067F89CC14862C, 31E96A93BF1A7CE1872A3CCDA6E07F86)
(ECCBC87E4B5CE2FE28308FD9F2A7BAF3, ADF6E4F1052BDE978344743CCDCF5771)
(E4DA3B7FBBCE2345D7772B0674A318D5, 0668FBCFE4098FEA0218163AC21E6531)
flags.txt
wc -l flags.txt 14776336 flags.txt
> head -n 5 flags.txt
utflag{aaaa}
utflag{aaab}
utflag{aaac}
utflag{aaad}
utflag{aaae}
> tail -n 5 flags.txt
utflag{9995}
utflag{9996}
utflag{9997}
utflag{9998}
utflag{9999}
アプローチ:ラグランジュ補間
問題文からSecret Sharingであることが分かります.
また,16進数で表された座標はMD5であることも確認できます.
(2, 5398141) (3, 5398288) (5, 5398756)
上記の座標を用いて,ラグランジュ補間を行うことでsecretを求めることができます.
ここでのsecretはflags.txtのsecret番目の文字列がflagであることを表していると考えられます.
以下,ソルバになります.
from Crypto.Util.number import long_to_bytes points = [(2, 5398141), (3, 5398288), (5, 5398756)] lag0 = (points[0][1] * points[1][0] * points[2][0]) // ((points[0][0]-points[1][0]) * (points[0][0]-points[2][0])) lag1 = (points[1][1] * points[0][0] * points[2][0]) // ((points[1][0]-points[0][0]) * (points[1][0]-points[2][0])) lag2 = (points[2][1] * points[1][0] * points[0][0]) // ((points[2][0]-points[1][0]) * (points[2][0]-points[0][0])) secret = lag0 + lag1 + lag2 print(secret) with open('flags.txt') as f: flags = [line.strip() for line in f.readlines()] print(flags[secret - 1])
> python solve.py
5398021
utflag{wOq0}
まとめ
- 久しぶりにWrite-up書けるくらい解けたので嬉しかった
- 裏でやってたzer0pts CTFほとんどできなかったので悲しかった
- 中級者レベルのCrypto問が安定して解けるようになったらRev, Pwnに手を出したい(これずっと言ってるじゃん)
チームメンバのWrite-up
線形合同法 (Linear Congruential Generators) によって生成される擬似乱数を予測する
はじめに
先日開催されたBSidesSF CTF 2020で線形合同法によって生成される擬似乱数を予測する問題 (mentalist) が出題されました.
この問題がとても勉強になったので,今回はこの問題を解く際に調べたことをまとめようと思います.
線形合同法とは
線形合同法とは,以下の漸化式で与えられる擬似乱数列の生成式です.
ここでのは定数であり,
,
,
,
を満たします.
class LCG: # X_{n+1} = (A \times X_n + B) \bmod M A = 9605000926055143081 # multiplier B = 9749676397194673813 # increment M = 18446744073709551615 # modulus def __init__(self, seed): # start value self.state = seed def next(self): self.state = (self.A * self.state + self.B) % self.M return self.state def get_parameters(self): return self.A, self.B, self.M def prediction_test(PRNGs, states, A, B, M): next_value = PRNGs.next() predicted_value = (A * states[-1] + B) % M for i, state in enumerate(states): print('X_{0}: {1}'.format(i, state)) print('\nnext value: {}'.format(next_value)) print('predicted value: {}'.format(predicted_value)) if next_value == predicted_value: print('correct!') else: print('incorrect!') def output_example(): states = [114514] PRNGs = LCG(states[0]) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) A, B, M = PRNGs.get_parameters() prediction_test(PRNGs, states, A, B, M)
X_0: 114514 X_1: 11263583670124855457 X_2: 4661627645215281165 X_3: 17524162438654086043 X_4: 6613605687528724796 next value: 13405047293276115594 predicted value: 13405047293276115594 correct!
擬似乱数の予測
線形合同法は,基本的に各パラメータ () と現在の疑似乱数 (
) が既知であれば,次の疑似乱数 (
) を簡単に求めることができます.
しかし,CTFで出題される線形合同法を使った問題では,各パラメータのどれかが未知であることがほとんどです(全てのパラメータが未知であることもある).
これから,CTFでよく出題される線形合同法を使った問題の擬似乱数を予測していきます.
B ( increment) が未知である場合
は既知であるとします.
# X_{n+1} = (A \times X_n + B) \bmod M A = 9605000926055143081 M = 18446744073709551615 X_0 = 17460462356393494334 X_1 = 5858263937153669472
このとき,次のようにしてを求めることができます.
以下は検証コードと出力結果です.
def solve_unknown_increment(states, A, M): B = (states[1] - A * states[0]) % M return B def test_unknown_increment(): print('test for unknown increment') # states = [getRandomNBitInteger(64)] states = [17460462356393494334] PRNGs = LCG(states[0]) states.append(PRNGs.next()) A, _, M = PRNGs.get_parameters() B = solve_unknown_increment(states, A, M) prediction_test(PRNGs, states, A, B, M)
test for unknown increment X_0: 17460462356393494334 X_1: 5858263937153669472 next value: 10449136789666358545 predicted value: 10449136789666358545 correct!
A (multiplier) と B ( increment) が未知である場合
は既知であるとします.
# X_{n+1} = (A \times X_n + B) \bmod M M = 18446744073709551615 X_0 = 16957592306608621537 X_1 = 8207823669407337095 X_2 = 3506114226401483223
このとき,次のようにしてを求めることができます.
と
の差分をとることで
を消します.
法上での
の逆元を
に乗じてあげることで
を求めることができます.
については,B ( increment) が未知である場合と同様に求めることができます.
はてなってpreタグ使わないとイコール揃えた数式使えないのか?
以下は検証コードと出力結果です.
from Crypto.Util.number import inverse def solve_unknown_multiplier(states, M): A = (states[2] - states[1]) * inverse((states[1] - states[0]), M) return A def test_unknown_multiplier(): print('test for unknown increment and multiplier') # states = [getRandomNBitInteger(64)] states = [16957592306608621537] PRNGs = LCG(states[0]) states.append(PRNGs.next()) states.append(PRNGs.next()) _, _, M = PRNGs.get_parameters() A = solve_unknown_multiplier(states, M) B = solve_unknown_increment(states, A, M) prediction_test(PRNGs, states, A, B, M)
test for unknown increment and multiplier X_0: 16957592306608621537 X_1: 8207823669407337095 X_2: 3506114226401483223 next value: 3098562741469012216 predicted value: 3098562741469012216 correct!
A (multiplier) と B ( increment) と M (modulus) が未知である場合
から
は既知であるとします.
X_0 = 12489966254767023172 X_1 = 3269246238714648380 X_2 = 9400253767069208013 X_3 = 18133428257392075756 X_4 = 4950164846933435189 X_5 = 13061720665666400352 X_6 = 15207628738950278065 X_7 = 10125779645391706253
このとき,次のようにしてを求めることができます.
上記の式は,以下のように表すこともできます.
つまり,のGCDを計算することで
を求めることができます.
しかし,今回の場合はが未知であるため,この方法で
を求めることができません.
そこで,法上で
の倍数(
)が
になること利用して,
を求めていきます.
まず始めに,と
の差分をとることにより
を消します.
次に差分同士の積の差分をとることによりを消します.
ここで,は,
となり,は,
となります.
そのため,は,
となります.
先述した通り,法上での
は
と等価であるため,
を
として扱うことができます.
したがって,のGCDを計算することで
を求めることできます.
はA (multiplier) と B ( increment) が未知である場合と同様に求めることができます.
以下は検証コードと出力結果です.
from Crypto.Util.number import inverse, GCD from functools import reduce def solve_unknown_modulus(states): diffs = [X_1 - X_0 for X_0, X_1 in zip(states, states[1:])] multiples_of_M = [T_2 * T_0 - T_1 ** 2 for T_0, T_1, T_2, in zip(diffs, diffs[1:], diffs[2:])] # GCD(GCD(multiples_of_M[0],multiples_of_M[1]), multiples_of_M[2]) M = reduce(GCD, multiples_of_M) return M def test_unknown_modulus(): print('test for unknown increment, multiplier and modulus') # states = [getRandomNBitInteger(64)] states = [12489966254767023172] PRNGs = LCG(states[0]) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) M = solve_unknown_modulus(states) A = solve_unknown_multiplier(states, M) B = solve_unknown_increment(states, A, M) prediction_test(PRNGs, states, A, B, M)
test for unknown increment, multiplier and modulus X_0: 12489966254767023172 X_1: 3269246238714648380 X_2: 9400253767069208013 X_3: 18133428257392075756 X_4: 4950164846933435189 X_5: 13061720665666400352 X_6: 15207628738950278065 X_7: 10125779645391706253 next value: 11999544724300060101 predicted value: 11999544724300060101 correct!
から
まで知ることができれば
を計算できますが,
が互いに素でない場合は
を上手く求められないので
程度まで利用したほうがいいと思います.
BSidesSF CTF 2020のmentalistのwrite-up
Can you read the mind of a computer?
mentalist-a05ae893.challenges.bsidessf.net:12345
> nc mentalist-a05ae893.challenges.bsidessf.net 12345
____
.'* *.'
__/_*_*(_
/ _______ \
_\_)/___\(_/_
/ _((\- -/))_ \
\ \())(-)(()/ /
' \(((()))/ '
/ ' \)).))/ ' \
/ _ \ - | - /_ \
( ( .;''';. .' )
_\"__ / HA )\ __"/_
\/ \ CK / \/
.' '...' ' )
/ / | \ \
/ . . . \
/ . . \
/ / | \ \
.' / . '. '.
_.-' / .. '-. '-._
_.-' | ... '-. '-.
(___________\____......'________)____)
_ _ ____ __ ___ __ _ _ ___ ___ _ _ __ ___ ___ __ _ __ __ _ ___
/ )( ( __| ) / __) \( \/ | __) / __) )( \/ \/ __| __| ( \ / \( ( ( __)
\ /\ /) _)/ (_( (_( O ) \/ \)_) ( (__) __ ( O )__ \)_)/ / ( O ) /)_)
(_/\_|____)___/\___)__/\_)(_(___) \___)_)(_/\__/(___(___)_)__) \__/\_)__|___)
Welcome Chosen One! I have been waiting for you...
The legend fortold of one that could read minds.
If you can read my mind I will reveal my great knowledge.
What number am I thinking of? 1
Actually I was thinking of 16056095589514, try again
What number am I thinking of? 1
No I'm sorry, I was thinking of 212251536946043
What number am I thinking of? 1
Hmmm no. My number was 134250435802692, are you sure you're okay?
What number am I thinking of? 1
I'm getting worried. I was thinking of 29371827723061; you're not doing so well.
What number am I thinking of? 1
I grow tired of your failures. My number was 189619676558750
What number am I thinking of? 1
Nope. 234022781299359 Perhaps you aren't the one I was waiting for?
What number am I thinking of? 1
WRONG! It was 136021856792488
What number am I thinking of? 1
My patience thins... 4394347413737 was my number
What number am I thinking of? 1
You're getting on my nerves. It was 113471694146706
What number am I thinking of? 1
I'm only going to give you one more chance. I was thinking of 185479241432995
What number am I thinking of? 1
I see now that you aren't who I was looking for.
It's too late now but I was thinking of 168630864482204
In case you were wondering how I was thinking of these numbers,
they were for the form x_n+1 = x_n * 207106347728281 + 5532122590609 % 249292453410000
And my initial seed x_0 was 60690097607505
With this you can verify that I wasn't cheating.
Good luck in your future endeavors!
A (multiplier) と B ( increment) と M (modulus) が未知である場合の線形合同法の問題です.
上記に示した方法で解くことができます.
def solve_mentalist(): states = [9726918447512, 46628235778441, 46641741588810, 26970189847019, 58978496575468, 18214530370557] M = solve_unknown_modulus(states) A = solve_unknown_multiplier(states, M) B = solve_unknown_increment(states, A, M) next_value = (A * states[-1] + B) % M print(next_value) next_value = (A * next_value + B) % M print(next_value)
21872728992686 53825285146255
Welcome Chosen One! I have been waiting for you...
The legend fortold of one that could read minds.
If you can read my mind I will reveal my great knowledge.
What number am I thinking of? 1
Actually I was thinking of 9726918447512, try again
What number am I thinking of? 1
No I'm sorry, I was thinking of 46628235778441
What number am I thinking of? 1
Hmmm no. My number was 46641741588810, are you sure you're okay?
What number am I thinking of? 1
I'm getting worried. I was thinking of 26970189847019; you're not doing so well.
What number am I thinking of? 1
I grow tired of your failures. My number was 58978496575468
What number am I thinking of? 1
Nope. 18214530370557 Perhaps you aren't the one I was waiting for?
What number am I thinking of? 21872728992686
Incredible! I WAS thinking of that number! But can you do it again?
What number am I thinking of? 53825285146255
You really are the one that was foretold. Please accept this knowldege:
CTF{rand_should_be_enough_for_anyone}
CTF{rand_should_be_enough_for_anyone}
おわりに
の求め方を理解したときは感動しました(法
上での
を作ってGCDに使うとこ).
以下が今回の検証(?)で使用したコードです.
from Crypto.Util.number import inverse, GCD, getRandomNBitInteger from functools import reduce class LCG: # X_{n+1} = (A \times X_n + B) \bmod M A = 9605000926055143081 # multiplier B = 9749676397194673813 # increment M = 18446744073709551615 # modulus def __init__(self, seed): # start value self.state = seed def next(self): self.state = (self.A * self.state + self.B) % self.M return self.state def get_parameters(self): return self.A, self.B, self.M def prediction_test(PRNGs, states, A, B, M): next_value = PRNGs.next() predicted_value = (A * states[-1] + B) % M for i, state in enumerate(states): print('X_{0}: {1}'.format(i, state)) print('\nnext value: {}'.format(next_value)) print('predicted value: {}'.format(predicted_value)) if next_value == predicted_value: print('correct!') else: print('incorrect!') def output_example(): states = [114514] PRNGs = LCG(states[0]) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) A, B, M = PRNGs.get_parameters() prediction_test(PRNGs, states, A, B, M) def solve_unknown_increment(states, A, M): B = (states[1] - A * states[0]) % M return B def test_unknown_increment(): print('test for unknown increment') states = [getRandomNBitInteger(64)] # states = [17460462356393494334] PRNGs = LCG(states[0]) states.append(PRNGs.next()) A, _, M = PRNGs.get_parameters() B = solve_unknown_increment(states, A, M) prediction_test(PRNGs, states, A, B, M) def solve_unknown_multiplier(states, M): A = (states[2] - states[1]) * inverse((states[1] - states[0]), M) return A def test_unknown_multiplier(): print('test for unknown increment and multiplier') states = [getRandomNBitInteger(64)] # states = [16957592306608621537] PRNGs = LCG(states[0]) states.append(PRNGs.next()) states.append(PRNGs.next()) _, _, M = PRNGs.get_parameters() A = solve_unknown_multiplier(states, M) B = solve_unknown_increment(states, A, M) prediction_test(PRNGs, states, A, B, M) def solve_unknown_modulus(states): diffs = [X_1 - X_0 for X_0, X_1 in zip(states, states[1:])] multiples_of_M = [T_2 * T_0 - T_1 ** 2 for T_0, T_1, T_2, in zip(diffs, diffs[1:], diffs[2:])] # GCD(GCD(multiples_of_M[0],multiples_of_M[1]), multiples_of_M[2]) M = reduce(GCD, multiples_of_M) return M def test_unknown_modulus(): print('test for unknown increment, multiplier and modulus') states = [getRandomNBitInteger(64)] # states = [12489966254767023172] PRNGs = LCG(states[0]) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) states.append(PRNGs.next()) M = solve_unknown_modulus(states) A = solve_unknown_multiplier(states, M) B = solve_unknown_increment(states, A, M) prediction_test(PRNGs, states, A, B, M) def solve_mentalist(): states = [9726918447512, 46628235778441, 46641741588810, 26970189847019, 58978496575468, 18214530370557] M = solve_unknown_modulus(states) A = solve_unknown_multiplier(states, M) B = solve_unknown_increment(states, A, M) next_value = (A * states[-1] + B) % M print(next_value) next_value = (A * next_value + B) % M print(next_value) def main(): output_example() # test_unknown_increment() # test_unknown_multiplier() # test_unknown_modulus() # solve_mentalist() if __name__ == '__main__': main()
参考文献
コンテスト中にこれをみての求め方を知りました.
nullcon HackIM Write-up
はじめに
2020/02/01 ~ 2019/02/03に開催されたHackTM CTFにチーム(NekochanNano!)で参加しました.
成績
チームとしては3問解いて160位でした (1208チーム中).
今回は自分が解いた1問のWrite-upを書きます.
Crypto
RockPaperScissors
To get the flag you have to beat us in rock paper scissors but to make it fair we used a commitment based scheme.
nc crypto1.ctf.nullcon.net 5000
rps.py
#!/usr/bin/env python3 from Crypto import Random from Crypto.Random import random from Crypto.Util.number import * from secret import flag sbox = [221, 229, 120, 8, 119, 143, 33, 79, 22, 93, 239, 118, 130, 12, 63, 207, 90, 240, 199, 20, 181, 4, 139, 98, 78, 32, 94, 108, 100, 223, 1, 173, 220, 238, 217, 152, 62, 121, 117, 132, 2, 55, 125, 6, 34, 201, 254, 0, 228, 48, 250, 193, 147, 248, 89, 127, 174, 210, 57, 38, 216, 225, 43, 15, 142, 66, 70, 177, 237, 169, 67, 192, 30, 236, 131, 158, 136, 159, 9, 148, 103, 179, 141, 11, 46, 234, 36, 18, 191, 52, 231, 23, 88, 145, 101, 17, 74, 44, 122, 75, 235, 175, 54, 40, 27, 109, 73, 202, 129, 215, 83, 186, 7, 163, 29, 115, 243, 13, 105, 184, 68, 124, 189, 39, 140, 138, 165, 219, 161, 150, 59, 233, 208, 226, 176, 144, 113, 146, 19, 224, 111, 126, 222, 178, 47, 252, 99, 87, 134, 249, 69, 198, 164, 203, 194, 170, 26, 137, 204, 157, 180, 168, 162, 56, 81, 253, 213, 45, 21, 58, 24, 171, 37, 82, 53, 50, 84, 196, 232, 242, 244, 64, 80, 10, 114, 212, 187, 205, 28, 51, 182, 16, 107, 245, 211, 85, 92, 195, 5, 197, 200, 31, 183, 61, 123, 86, 167, 154, 41, 151, 35, 247, 246, 153, 95, 206, 149, 76, 112, 71, 230, 106, 188, 172, 241, 72, 156, 49, 14, 214, 155, 110, 102, 116, 128, 160, 135, 104, 77, 91, 190, 60, 42, 185, 96, 97, 251, 218, 133, 209, 65, 227, 3, 166, 255, 25] p = [5, 9, 1, 8, 3, 11, 0, 12, 7, 4, 14, 13, 10, 15, 6, 2] round = 16 def pad(data, size = 16): pad_byte = (size - len(data) % size) % size data = data + bytearray([pad_byte]) * pad_byte return data def repeated_xor(p, k): return bytearray([p[i] ^ k[i % len(k)] for i in range(len(p))]) def bytes_to_int(xbytes): return bytes_to_long(xbytes) def int_to_bytes(x): return long_to_bytes(x, 16) def group(input, size = 16): return [input[i * size: (i + 1) * size] for i in range(len(input) // size)] def hash(data): state = bytearray([208, 151, 71, 15, 101, 206, 50, 225, 223, 14, 14, 106, 22, 40, 20, 2]) data = pad(data, 16) data = group(data) for roundkey in data: for _ in range(round): state = repeated_xor(state, roundkey) for i in range(len(state)): state[i] = sbox[state[i]] temp = bytearray(16) for i in range(len(state)): temp[p[i]] = state[i] state = temp return hex(bytes_to_int(state))[2:] def gen_commitments(): secret = bytearray(Random.get_random_bytes(16)) rc = hash(secret + b"r") pc = hash(secret + b"p") sc = hash(secret + b"s") secret = hex(bytes_to_int(secret))[2:] rps = [("r", rc), ("p", pc), ("s", sc)] random.shuffle(rps) return secret, rps def check_win(a, b): if a == "r": if b == "p": return True else: return False elif a == "s": if b == "r": return True else: return False elif a == "p": if b == "s": return True else: return False return False def main(): print("Beat me in Rock Paper Scissors 20 consecutive times to get the flag") for i in range(20): secret, rps = gen_commitments() move = rps[0][0] print("Here are the possible commitments, the first one is my move:", " ".join(map(lambda s: s[1], rps))) inp = input("Your move:") res = check_win(move, inp) print("My move was:", move, "Secret was:", secret) if not res: print("You lose!") exit(0) print("You win") print("Your reward is", flag) exit(0) if __name__ == '__main__': main()
> nc crypto1.ctf.nullcon.net 5000 Beat me in Rock Paper Scissors 20 consecutive times to get the flag Here are the possible commitments, the first one is my move: fce244bcbc04700b41826ca483c023f9 d81237fe4e8bed3cf9e7a92291675454 5cb149b74cb5c739082c3775a885fac4 Your move:r My move was: s Secret was: 28351b948c17fb2b1604602c0423c693 Here are the possible commitments, the first one is my move: d33f53586f3061727da1ba5153d069be 3aabc6c958fa1ff562d6fe5ef57e6493 cd42da2f16c1173e39d196f8edf8becf Your move:r My move was: p Secret was: 101e48d532eec3d49f3df1386a52d14a You lose!
アプローチ:hash()の逆関数を書いてstateを求める
rps.pyの処理を簡単にまとめると以下のようになります.
- 16byteの
secretを生成 secret + r,secret + p,secret + sそれぞれのハッシュ値を生成stateの初期化- 入力データを16の倍数にpadding
- padding済みデータを16byteに分割
roundkey(16byteに分割されたpadding済みデータ) ごとにstateに対するxor, 置換, 転置を16round繰り返すroundkeyとstateのxorを計算sbox(substitution box) によってstateを置換pによってstateを転置
- 最後に
stateをハッシュ値としてreturn
hash(secret + r),hash(secret + p),hash(secret + s)をシャッフル- シャッフル結果を出力
- シャッフル結果の先頭に勝てる
moveを入力 (r,pors) - 20連勝するとflag
以上のことから,この問題では出力されたハッシュ値からmoveを特定する必要があることが分かります.
そのためには,hash()の逆関数を作成し,roundkeyをsecretとしたときのstateを求める必要があります.
roundkeyをsecretとしたときのstateは,2つめのroundkey (入力データの17byteから32byte)がpad(), group()によって[move]\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0fになることを利用して求めることができます.
つまり,全てのハッシュ値に対してroundkeyをr\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f, p\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f, s\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0fとしたときのstateを求め,
全てのハッシュ値に共通するstateを見つけることで,そのハッシュ値がどのmoveから生成されたものなのかを特定できます.
以下ソルバになります(汚い)
from Crypto import Random from Crypto.Random import random from Crypto.Util.number import * from socket import * rev_sbox = [47, 30, 40, 252, 21, 198, 43, 112, 3, 78, 183, 83, 13, 117, 228, 63, 191, 95, 87, 138, 19, 168, 8, 91, 170, 255, 156, 104, 188, 114, 72, 201, 25, 6, 44, 210, 86, 172, 59, 123, 103, 208, 242, 62, 97, 167, 84, 144, 49, 227, 175, 189, 89, 174, 102, 41, 163, 58, 169, 130, 241, 203, 36, 14, 181, 250, 65, 70, 120, 150, 66, 219, 225, 106, 96, 99, 217, 238, 24, 7, 182, 164, 173, 110, 176, 195, 205, 147, 92, 54, 16, 239, 196, 9, 26, 214, 244, 245, 23, 146, 28, 94, 232, 80, 237, 118, 221, 192, 27, 105, 231, 140, 218, 136, 184, 115, 233, 38, 11, 4, 2, 37, 98, 204, 121, 42, 141, 55, 234, 108, 12, 74, 39, 248, 148, 236, 76, 157, 125, 22, 124, 82, 64, 5, 135, 93, 137, 52, 79, 216, 129, 209, 35, 213, 207, 230, 226, 159, 75, 77, 235, 128, 162, 113, 152, 126, 253, 206, 161, 69, 155, 171, 223, 31, 56, 101, 134, 67, 143, 81, 160, 20, 190, 202, 119, 243, 111, 186, 222, 122, 240, 88, 71, 51, 154, 197, 177, 199, 151, 18, 200, 45, 107, 153, 158, 187, 215, 15, 132, 249, 57, 194, 185, 166, 229, 109, 60, 34, 247, 127, 32, 0, 142, 29, 139, 61, 133, 251, 48, 1, 220, 90, 178, 131, 85, 100, 73, 68, 33, 10, 17, 224, 179, 116, 180, 193, 212, 211, 53, 149, 50, 246, 145, 165, 46, 254] rev_p = [6, 2, 15, 4, 9, 0, 14, 8, 3, 1, 12, 5, 7, 11, 10, 13] round = 16 def pad(data, size = 16): pad_byte = (size - len(data) % size) % size data = data + bytearray([pad_byte]) * pad_byte return data def group(input, size = 16): return [input[i * size: (i + 1) * size] for i in range(len(input) // size)] def repeated_xor(p, k): return bytearray([p[i] ^ k[i % len(k)] for i in range(len(p))]) def rev_hash(rps_hash): while len(rps_hash) < 32: rps_hash = '0' + rps_hash r = b'r\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f' p = b'p\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f' s = b's\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f\x0f' roundkeys = [r, p, s] states = [] for roundkey in roundkeys: state = bytearray([int(rps_hash[i:i+2],16) for i in range(0,len(rps_hash),2)]) for _ in range(round): temp = bytearray(16) for i in range(len(state)): temp[rev_p[i]] = state[i] state = temp for i in range(len(state)): state[i] = rev_sbox[state[i]] state = repeated_xor(state,roundkey) # print(state) states.append(state) return states sock = socket(AF_INET, SOCK_STREAM) sock.connect(('crypto1.ctf.nullcon.net', 5000)) for _ in range(21): rec = sock.recv(1024).decode('utf-8') print(rec) commitments = rec.split('\n')[1].split(': ')[1].split(' ') rev_hash_result = [] for commitment in commitments: rev_hash_result.append(rev_hash(commitment)) ans = [1 if x in rev_hash_result[1] and x in rev_hash_result[2] else 0 for x in rev_hash_result[0]] if ans == [1, 0, 0]: sock.send(b'p\n') elif ans == [0, 1, 0]: sock.send(b's\n') else: sock.send(b'r\n')
hackim20{b4d_pr1mitiv3_beats_all!1!_7f65}
まとめ
- 何もわからなかった
- ayyMessage(Crypto), SecureLinearFunctionEvaluation(Crypto), returminator(Rev)解きたかった…
HackTM CTF 2020 Write-up
はじめに
2020/02/01 ~ 2019/02/03に開催されたHackTM CTFにチーム(NekochanNano!)で参加しました.
成績
チームとしては5問解いて171位でした (747チーム中).
今回は自分が解いた3問のWrite-upを書きます.
Crypto
RSA is easy #1 [50pts, 279solved]
rsa.py
import random from my_math import next_prime from flag import flag def egcd(a, b): x, y, u, v = 0, 1, 1, 0 while a != 0: q, r = b//a, b % a m, n = x-u*q, y-v*q b, a, x, y, u, v = a, r, u, v, m, n gcd = b return gcd, x, y def gen_keys(p, q): e = 65537 n = p * q phi = (p - 1) * (q - 1) gcd, d, b = egcd(e, phi) # Keys:((pub), (priv)) return ((e, n), (d, n)) def enc(key, p): e, n = key cipher = [pow(ord(char), e, n) for char in p] return cipher def dec(pk, c): key, n = pk plain = [chr(pow(char, key, n)) for char in c] return ''.join(plain) p = next_prime(random.SystemRandom().getrandbits(512)) q = next_prime(random.SystemRandom().getrandbits(512)) flag_key=gen_keys(p, q) print("Public key:") print(flag_key[0]) flag_c=(enc(flag_key[0], flag)) print("Encrypted flag:") print(flag_c)
c
Public key: (65537, 28150970547901913019901824364390497053600856369839321617996700606130553862041378369018779003752433356889118526332329074054728613209407037089320809898343953157935211086135010436283805891893636870991411236307901650696221491790470635225076251966300189483160148297407974155121570252648252906976186499329924342873) Encrypted flag: [24603931406187071861602497345394097692989773194039735745762181586628499407802825983901643034231448504738113184470035863824128031443012073830520233613935485192804104698999763287388765215634314977991988580048221541560353418280294402691661980705832590960497587810514295642811714680627768268704899874164681718449, 11226318059664066669163529308725576208632153806776762372429671026861927737060205604020741904348343722215670471225630839065129589767356765848271000166982882271636977663052775953958080543340165408211633442938366994031562890034541604362383645601883118173819506187865617998294930587997187071040181458961091560176, 15645290594995180815865397749136800126080704684884296404807344870555186823350216705796063922278419585484662234210001661578549560411864952462380096494781766394542247609648743673312823946783517115542404474786395934886667795692210287283039316418126796934535150832709500306153601987121172178183970841498331059732, 24345863558959407738249127568820138362115734211146549194534219311913032290216606859385934708675962835857804566049600710875035366973110422262131331932310524891713319358676673958738776644229757625523955354996402750265022578843637525183704187498194489645838490640529841182709661371499013082259193633000753627261, 9620679224297488175028367924764722982789333194446063577221477359704180638294602848741035585656113543497776415635770748468725814916994577398023154224563920936523717884116880223345204061598438291740007518025998041449406726084042681798053863495542392481059281588020105313791046017356493739244555377217866496734, 1681724029430984846089508679185107538104072555994133932050319175633667369916570440070548756805254789524599169177371471218251246349461689959989338169394649813424706418737543924129213419625988100326558802566046751879531469160120914735332858786199496335523515150741728027296830843112416558460932541777024522279, 20629854768856798537062426042570334097651328955665698429979954410631113160492201197690192324881508105172595216229624523572595589920695165876501026993810936392510720968159305964832449680889041278532807173859579419197780294984519222830572413180237776797800176462492384318120546495539728732366110782215071262307, 7440918084186181327822271261394344901791253526257166181264874776746516620936925799031445704193589071453959493392065321806281801023425299535553522582376879027448581379760896052013060957519595664095702210758316558762834545655992756483227787274192094065257224706388623944855362716578806372564148647945479173348, 5097867843777034076271397095201528351784693372027998615436445410912131141882225577577253530396333413579756394884096318434100382509189974240357351425474190558456256750742731090012822064840481143528081027106843123030275420215136304130321013605031261372665636366377162666476737296028608455229357416005773064242, 10420107412794383499391199999666100864853724770814620968725971207705900061273163202891569477729023724554388008575891113425781557296798472693974759813058067631655217722786373465395279381307973425004404348124524059844749313287030234750535347511172780349725636807760402334957881556461382950021814486095167001394, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 11226318059664066669163529308725576208632153806776762372429671026861927737060205604020741904348343722215670471225630839065129589767356765848271000166982882271636977663052775953958080543340165408211633442938366994031562890034541604362383645601883118173819506187865617998294930587997187071040181458961091560176, 16657126895659048065404729920028465477385009450133540950695155983380795627778054526133891673615252510518969355629562948102050307259107355106086468465392660721567070464708776158039303608428552547481825035736610837329720474688421062759594907620576318249542577396722737724172954532394471909440668625218820801756, 11113777356910731413424023299582648618258376222028450254478672148119889617557563576704932635131420845868165014982665717620845578039880527701593963719893467068820107811384041511295664833904504511210342105242330522375476482706044695838957591685781703894244561607764476555630573446589408768780659378128082633769, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 1681724029430984846089508679185107538104072555994133932050319175633667369916570440070548756805254789524599169177371471218251246349461689959989338169394649813424706418737543924129213419625988100326558802566046751879531469160120914735332858786199496335523515150741728027296830843112416558460932541777024522279, 5237767970074646857079948735567615361735616179074197239639640947679550920349684166643572837235712904929824521258264241503059989875517915784117038966236672390569320206379357882906463342282254405974383459878863044723383164329146669331810709270455492110346838097216174137176255793792848357953314563364460847842, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 2141625583250052666579569568613448089970148215959031795439930595139028085767825695294403905882459409861220995951141855281841435481587946825079031782977651718402048988278639212978854590412709087674713750292922397103941195760574072700517109381299788645871729355745594573785064162048047595009933642068871994670, 278354276293884030290100330445865286604723740111170856624965259573282278044823323212960304154629174664076141280100412502135750130875356944835909175355370317285768658282746817782130476757714384697086179400629156643250500432197002583758692394681401772203578628635926749457621478296182304772136118691761841359, 6039667595601233082552071610487048398346324705021423176423484623705376133358539134558362499891954091431687578305623106726900655384011241742715735786166290331136153240702822544221903404870992713778423167867663948083662620087859096707381620051266745156545213726214080049764382107442159825610310695543673475542, 21353765873487781085375016306418205544750755310255410963646737671193146222650262290683259548572190880304009015662963424520575937651278866672082973874806201031606257157229306007587966460187818647603633973019548401357989358306250139692325474674826791149726161678649996852062656272851387461089863388359261125336, 11226318059664066669163529308725576208632153806776762372429671026861927737060205604020741904348343722215670471225630839065129589767356765848271000166982882271636977663052775953958080543340165408211633442938366994031562890034541604362383645601883118173819506187865617998294930587997187071040181458961091560176, 20576388598886140095325204584799302384454378372204683348252463729525849583734948105765087991438423260690623246579570440405616572326057536248148020737810766134083795050076636686776809469271643188562482921546497071402873405706504773345621716428511481598704631451463399778602486417840466985891815649711178813963, 17347447662661486040040289855519394974371562320877472776529836975445205017304164550202099250096382852783253959549113036367974281750823938616836362593312254792770954856762797438690474329666549947795964992533463700161635382925555835347885819042031312006167190561233042383984087765920275010577545908085026177611, 11788628214684738246695632901992250075758959059858474645166125685861157046466064692980236734739634298802473894878268029860203026238925142258303727438570051822763330338744774300757888262747314093511013562545738571326771345495509434761853742569509480619380000424215527153118231084573851377049921456961916278761, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 2141625583250052666579569568613448089970148215959031795439930595139028085767825695294403905882459409861220995951141855281841435481587946825079031782977651718402048988278639212978854590412709087674713750292922397103941195760574072700517109381299788645871729355745594573785064162048047595009933642068871994670, 2710029303357232932696197225263692040597986927359269224740812600224998707144266259851604978553286889767425982708691908438984279442981540971935737617354609856642312100797081348174935195638083002333058089328102430432526612805955273581245352312630845237670744276402867230550537275379675828467791243032108754996, 19981107233593350929447953514006501458466479260151660185153999799085657467921097940751860717309377498501638075002136637344148955811617399850718322497572421311807629329642551519284713638882025500074565475569618691516951449764680555447185364165687596161053684299589053909233984617244886185728811651967713024530, 3975884358027162862622932959187611984655247354547659825042810425039322096401899672988989768997134724085482147901304365437476311647149733392577446833370358728610677436154877051592307539990184750467273668379065865808900410057533079113476991204462719784464847498582643056503810805516315622314948257403761762299, 6039667595601233082552071610487048398346324705021423176423484623705376133358539134558362499891954091431687578305623106726900655384011241742715735786166290331136153240702822544221903404870992713778423167867663948083662620087859096707381620051266745156545213726214080049764382107442159825610310695543673475542, 14296542628093736444815382636071360035549021313467366701986569710120268508807886041986007828960248665683292143486565404978073122476968882030310174125355932205646388813061197657253533595700948593692407928813318978600474254105007396254987998953819782624738628334271910759242195864082910860797444993756044746481, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 7983594351048693624291138893287137601848867970873700373034058935656045095987011116108642350616654713531373295621458596238107660073931212524833777531450461876588350132328332972361857441613098452082271331281504722310376573085001395356078670960667878342134517577992585442881605030717788248137764480486762452442, 7983594351048693624291138893287137601848867970873700373034058935656045095987011116108642350616654713531373295621458596238107660073931212524833777531450461876588350132328332972361857441613098452082271331281504722310376573085001395356078670960667878342134517577992585442881605030717788248137764480486762452442, 23267174349531278768420819619439317179083929128083924515569762521057285892931325108327037262091624670335579302436476096123152288550738706103166820604983405317430467198343871458522070337902643863890959573514405066297449924638838605501211486861582957963752388608487593217237563529201436917108304692859773404548]
アプローチ:文字空間を全探索
rsa.pyのenc()ではflagを1文字ずつ暗号化しています.
そのため,文字を1文字ずつ暗号化し,Encrypted flagと比較することで,平文を特定できます.
以下ソルバです.
import string e, n = 65537, 28150970547901913019901824364390497053600856369839321617996700606130553862041378369018779003752433356889118526332329074054728613209407037089320809898343953157935211086135010436283805891893636870991411236307901650696221491790470635225076251966300189483160148297407974155121570252648252906976186499329924342873 encs = [24603931406187071861602497345394097692989773194039735745762181586628499407802825983901643034231448504738113184470035863824128031443012073830520233613935485192804104698999763287388765215634314977991988580048221541560353418280294402691661980705832590960497587810514295642811714680627768268704899874164681718449, 11226318059664066669163529308725576208632153806776762372429671026861927737060205604020741904348343722215670471225630839065129589767356765848271000166982882271636977663052775953958080543340165408211633442938366994031562890034541604362383645601883118173819506187865617998294930587997187071040181458961091560176, 15645290594995180815865397749136800126080704684884296404807344870555186823350216705796063922278419585484662234210001661578549560411864952462380096494781766394542247609648743673312823946783517115542404474786395934886667795692210287283039316418126796934535150832709500306153601987121172178183970841498331059732, 24345863558959407738249127568820138362115734211146549194534219311913032290216606859385934708675962835857804566049600710875035366973110422262131331932310524891713319358676673958738776644229757625523955354996402750265022578843637525183704187498194489645838490640529841182709661371499013082259193633000753627261, 9620679224297488175028367924764722982789333194446063577221477359704180638294602848741035585656113543497776415635770748468725814916994577398023154224563920936523717884116880223345204061598438291740007518025998041449406726084042681798053863495542392481059281588020105313791046017356493739244555377217866496734, 1681724029430984846089508679185107538104072555994133932050319175633667369916570440070548756805254789524599169177371471218251246349461689959989338169394649813424706418737543924129213419625988100326558802566046751879531469160120914735332858786199496335523515150741728027296830843112416558460932541777024522279, 20629854768856798537062426042570334097651328955665698429979954410631113160492201197690192324881508105172595216229624523572595589920695165876501026993810936392510720968159305964832449680889041278532807173859579419197780294984519222830572413180237776797800176462492384318120546495539728732366110782215071262307, 7440918084186181327822271261394344901791253526257166181264874776746516620936925799031445704193589071453959493392065321806281801023425299535553522582376879027448581379760896052013060957519595664095702210758316558762834545655992756483227787274192094065257224706388623944855362716578806372564148647945479173348, 5097867843777034076271397095201528351784693372027998615436445410912131141882225577577253530396333413579756394884096318434100382509189974240357351425474190558456256750742731090012822064840481143528081027106843123030275420215136304130321013605031261372665636366377162666476737296028608455229357416005773064242, 10420107412794383499391199999666100864853724770814620968725971207705900061273163202891569477729023724554388008575891113425781557296798472693974759813058067631655217722786373465395279381307973425004404348124524059844749313287030234750535347511172780349725636807760402334957881556461382950021814486095167001394, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 11226318059664066669163529308725576208632153806776762372429671026861927737060205604020741904348343722215670471225630839065129589767356765848271000166982882271636977663052775953958080543340165408211633442938366994031562890034541604362383645601883118173819506187865617998294930587997187071040181458961091560176, 16657126895659048065404729920028465477385009450133540950695155983380795627778054526133891673615252510518969355629562948102050307259107355106086468465392660721567070464708776158039303608428552547481825035736610837329720474688421062759594907620576318249542577396722737724172954532394471909440668625218820801756, 11113777356910731413424023299582648618258376222028450254478672148119889617557563576704932635131420845868165014982665717620845578039880527701593963719893467068820107811384041511295664833904504511210342105242330522375476482706044695838957591685781703894244561607764476555630573446589408768780659378128082633769, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 1681724029430984846089508679185107538104072555994133932050319175633667369916570440070548756805254789524599169177371471218251246349461689959989338169394649813424706418737543924129213419625988100326558802566046751879531469160120914735332858786199496335523515150741728027296830843112416558460932541777024522279, 5237767970074646857079948735567615361735616179074197239639640947679550920349684166643572837235712904929824521258264241503059989875517915784117038966236672390569320206379357882906463342282254405974383459878863044723383164329146669331810709270455492110346838097216174137176255793792848357953314563364460847842, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 2141625583250052666579569568613448089970148215959031795439930595139028085767825695294403905882459409861220995951141855281841435481587946825079031782977651718402048988278639212978854590412709087674713750292922397103941195760574072700517109381299788645871729355745594573785064162048047595009933642068871994670, 278354276293884030290100330445865286604723740111170856624965259573282278044823323212960304154629174664076141280100412502135750130875356944835909175355370317285768658282746817782130476757714384697086179400629156643250500432197002583758692394681401772203578628635926749457621478296182304772136118691761841359, 6039667595601233082552071610487048398346324705021423176423484623705376133358539134558362499891954091431687578305623106726900655384011241742715735786166290331136153240702822544221903404870992713778423167867663948083662620087859096707381620051266745156545213726214080049764382107442159825610310695543673475542, 21353765873487781085375016306418205544750755310255410963646737671193146222650262290683259548572190880304009015662963424520575937651278866672082973874806201031606257157229306007587966460187818647603633973019548401357989358306250139692325474674826791149726161678649996852062656272851387461089863388359261125336, 11226318059664066669163529308725576208632153806776762372429671026861927737060205604020741904348343722215670471225630839065129589767356765848271000166982882271636977663052775953958080543340165408211633442938366994031562890034541604362383645601883118173819506187865617998294930587997187071040181458961091560176, 20576388598886140095325204584799302384454378372204683348252463729525849583734948105765087991438423260690623246579570440405616572326057536248148020737810766134083795050076636686776809469271643188562482921546497071402873405706504773345621716428511481598704631451463399778602486417840466985891815649711178813963, 17347447662661486040040289855519394974371562320877472776529836975445205017304164550202099250096382852783253959549113036367974281750823938616836362593312254792770954856762797438690474329666549947795964992533463700161635382925555835347885819042031312006167190561233042383984087765920275010577545908085026177611, 11788628214684738246695632901992250075758959059858474645166125685861157046466064692980236734739634298802473894878268029860203026238925142258303727438570051822763330338744774300757888262747314093511013562545738571326771345495509434761853742569509480619380000424215527153118231084573851377049921456961916278761, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 2141625583250052666579569568613448089970148215959031795439930595139028085767825695294403905882459409861220995951141855281841435481587946825079031782977651718402048988278639212978854590412709087674713750292922397103941195760574072700517109381299788645871729355745594573785064162048047595009933642068871994670, 2710029303357232932696197225263692040597986927359269224740812600224998707144266259851604978553286889767425982708691908438984279442981540971935737617354609856642312100797081348174935195638083002333058089328102430432526612805955273581245352312630845237670744276402867230550537275379675828467791243032108754996, 19981107233593350929447953514006501458466479260151660185153999799085657467921097940751860717309377498501638075002136637344148955811617399850718322497572421311807629329642551519284713638882025500074565475569618691516951449764680555447185364165687596161053684299589053909233984617244886185728811651967713024530, 3975884358027162862622932959187611984655247354547659825042810425039322096401899672988989768997134724085482147901304365437476311647149733392577446833370358728610677436154877051592307539990184750467273668379065865808900410057533079113476991204462719784464847498582643056503810805516315622314948257403761762299, 6039667595601233082552071610487048398346324705021423176423484623705376133358539134558362499891954091431687578305623106726900655384011241742715735786166290331136153240702822544221903404870992713778423167867663948083662620087859096707381620051266745156545213726214080049764382107442159825610310695543673475542, 14296542628093736444815382636071360035549021313467366701986569710120268508807886041986007828960248665683292143486565404978073122476968882030310174125355932205646388813061197657253533595700948593692407928813318978600474254105007396254987998953819782624738628334271910759242195864082910860797444993756044746481, 20895198446192697825002890636650624361863759520944494391240191454443921345578043873584884838772334163748883476104011030592329948454531053024873263786017045083052443924403769542324123323834338391361149767913830998218951574784777785739566046139742309557536025214334831372509789246522325522982945241815388133477, 7983594351048693624291138893287137601848867970873700373034058935656045095987011116108642350616654713531373295621458596238107660073931212524833777531450461876588350132328332972361857441613098452082271331281504722310376573085001395356078670960667878342134517577992585442881605030717788248137764480486762452442, 7983594351048693624291138893287137601848867970873700373034058935656045095987011116108642350616654713531373295621458596238107660073931212524833777531450461876588350132328332972361857441613098452082271331281504722310376573085001395356078670960667878342134517577992585442881605030717788248137764480486762452442, 23267174349531278768420819619439317179083929128083924515569762521057285892931325108327037262091624670335579302436476096123152288550738706103166820604983405317430467198343871458522070337902643863890959573514405066297449924638838605501211486861582957963752388608487593217237563529201436917108304692859773404548] flag = '' for enc in encs: for x in string.printable: if pow(ord(x),e,n) == enc: flag += x break print(flag)
> python solve.py
HackTM{why_ar3_MY_pR1va7es_pu8l1C_??}
HackTM{why_ar3_MY_pR1va7es_pu8l1C_??}
RSA is easy #2 [50pts, 157solved]
Provide the flag in this format:
HackTM{words_you_found}
Example:
If you find "i am a flag"
submit:
HackTM{i_am_a_flag}
rsa.py
import random from my_math import next_prime from flag import flag def egcd(a, b): x, y, u, v = 0, 1, 1, 0 while a != 0: q, r = b//a, b % a m, n = x-u*q, y-v*q b, a, x, y, u, v = a, r, u, v, m, n gcd = b return gcd, x, y def gen_keys(p, q): e = 65537 n = p * q phi = (p - 1) * (q - 1) gcd, d, b = egcd(e, phi) # Keys:((pub), (priv)) return ((e, n), (d, n)) def enc(key, p): e, n = key cipher = [pow(ord(char), e, n) for char in p] return cipher def dec(pk, c): key, n = pk plain = [chr(pow(char, key, n)) for char in c] return ''.join(plain) p = next_prime(random.SystemRandom().getrandbits(512)) q = next_prime(random.SystemRandom().getrandbits(512)) flag_key=gen_keys(p, q) print("Public key:") print(flag_key[0]) flag_c=(enc(flag_key[0], flag)) print("Encrypted flag:") print(flag_c)
c
Public key: [DATA CORRUPTED] Encrypted flag: [34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 22898825038689625715487339309684047496088088286379048682632329486928624317960893419908872575544541743109960984821146081005860923057711786824611353925189608095318119267730739890712604642525421504696090823029339278724706589872240410882755614978083387780278129076143536569517954666638462991000336176075614807880, 32673744615799712487218586784858666657615496658878295924699304141157435241805321678825497057203170526047413088723755930727839423037832480520297361079311603101279858983310265841651031957166707800564192379099456051456890378670008176632913201998572911894331423107676669652519124282681545581828946130363768378027, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 39071839511948638988080907036852746654085273366404837973213329692814484554408908523546999438831321352816110395822192272922701572846039352688552458816923896373772472819785936751685465282644216513301671688378689515602296293965301386883552780271126801778759956341143215735911106078099952795281272294184101222894, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 52840621689121797895256363389338274694450461789829175087736646052885972599541176587393339836186116798179639665528641843475425650830795547188378088601848535424795824136246287654182750346069524432086206082201048105736692531622222816403756012329174735009131234941877426201644907061786470186383501136594209222405, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 52840621689121797895256363389338274694450461789829175087736646052885972599541176587393339836186116798179639665528641843475425650830795547188378088601848535424795824136246287654182750346069524432086206082201048105736692531622222816403756012329174735009131234941877426201644907061786470186383501136594209222405, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 38802989341210530457378237385843973124921316122128304138276723482825938449328688522058677634210417960328667542939425659386994898427574509818766303473446802692515345332427976398389916234534200995301483992776549890379656184952685366723722458147873775598641647772939243953968981681779761004069962129149532525241, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 52840621689121797895256363389338274694450461789829175087736646052885972599541176587393339836186116798179639665528641843475425650830795547188378088601848535424795824136246287654182750346069524432086206082201048105736692531622222816403756012329174735009131234941877426201644907061786470186383501136594209222405, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 39071839511948638988080907036852746654085273366404837973213329692814484554408908523546999438831321352816110395822192272922701572846039352688552458816923896373772472819785936751685465282644216513301671688378689515602296293965301386883552780271126801778759956341143215735911106078099952795281272294184101222894, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 50154500011327049415150110613714558756986965132059956858621967629544808661996323441483612798709196285670748400127394046198652122647065373883652074401488461140240807698457285933739509452128499026773680398001271333305476126787388797879767072284116978372707084228927669307533874093727830120482310649071798909223, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 39071839511948638988080907036852746654085273366404837973213329692814484554408908523546999438831321352816110395822192272922701572846039352688552458816923896373772472819785936751685465282644216513301671688378689515602296293965301386883552780271126801778759956341143215735911106078099952795281272294184101222894, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 52840621689121797895256363389338274694450461789829175087736646052885972599541176587393339836186116798179639665528641843475425650830795547188378088601848535424795824136246287654182750346069524432086206082201048105736692531622222816403756012329174735009131234941877426201644907061786470186383501136594209222405, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 39071839511948638988080907036852746654085273366404837973213329692814484554408908523546999438831321352816110395822192272922701572846039352688552458816923896373772472819785936751685465282644216513301671688378689515602296293965301386883552780271126801778759956341143215735911106078099952795281272294184101222894, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 50154500011327049415150110613714558756986965132059956858621967629544808661996323441483612798709196285670748400127394046198652122647065373883652074401488461140240807698457285933739509452128499026773680398001271333305476126787388797879767072284116978372707084228927669307533874093727830120482310649071798909223, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 38802989341210530457378237385843973124921316122128304138276723482825938449328688522058677634210417960328667542939425659386994898427574509818766303473446802692515345332427976398389916234534200995301483992776549890379656184952685366723722458147873775598641647772939243953968981681779761004069962129149532525241, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 50154500011327049415150110613714558756986965132059956858621967629544808661996323441483612798709196285670748400127394046198652122647065373883652074401488461140240807698457285933739509452128499026773680398001271333305476126787388797879767072284116978372707084228927669307533874093727830120482310649071798909223, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 52840621689121797895256363389338274694450461789829175087736646052885972599541176587393339836186116798179639665528641843475425650830795547188378088601848535424795824136246287654182750346069524432086206082201048105736692531622222816403756012329174735009131234941877426201644907061786470186383501136594209222405, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 47570760099332538630074246588266937941307517820515142582135658748192399272005539496578959306267521195254022986091052760574620123103280649808061816984656151624030812710123783651478012545264847339309664114861788542619162083048255751820685971177031319072241032895991001430158963380558156843892347920250300986171, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 930044605345939201480478373277413008095802574786191190905074555539638928544692229073288242327962810058855318227403376039279203240132190223148619950893934472181209933145274613718642434124893448103578245304758494945314633484270441574356508120432815219715951750624307928142686494962369790708881847436477126536, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 50154500011327049415150110613714558756986965132059956858621967629544808661996323441483612798709196285670748400127394046198652122647065373883652074401488461140240807698457285933739509452128499026773680398001271333305476126787388797879767072284116978372707084228927669307533874093727830120482310649071798909223, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524, 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103, 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336, 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472, 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889, 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582, 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151, 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832, 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799]
アプローチ:Encrypted flagを換字式暗号として考える
RSA is easy #2はRSA is easy #1から公開鍵情報を削除した問題です.
他に,RSA is easy #1との相違点を探すとEncrypted flagが非常に長くなっていることが分かります.
このことから,文字の出現頻度を利用したアプローチを行えます.
import string from collections import Counter with open('cipher.txt') as f: ciphers = list(map(int,f.read().strip().split(','))) for cipher, freq in Counter(ciphers).most_common(): print(freq, cipher)
177 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582 123 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909 83 20615543970401106049899252800192288457964182639045355076454473284260002293725082025968310990122731962791617789632077170719345622736070264054367958868239517799808416688171918069309633316391105904609498475463756359094918228354423745819313393742987851160846772360092594149040683896814298190633249373326376461156 66 11754165346287637561545259343840422291909328839266777034181425212469224088636786285072037265988741867852390393052619139981204304725012657494805876058735252784205208373103211292641197325597338249663286939455864193037451288723183790294305055993067129506821935556455779063943868491706701650087037910887657226493 64 1616691599456040168445566414573196426135242040353418621535727203361763119546110811202180542592381606989262060743706931509368561992575755611142039943697929675456007056209371231656367986288172877583606660982468769562130680078575424889216776816820937295397087401890122017587798820436843206222029244517132787091 61 39385543283404473075185452058079832095584936856222212380734415975432643784664927411933026085735951287828134889813409092456274531550067215917681707367020221976856074609811863093935500364044953252851773508292484565675960979638799629224447070845682042579853348896232929185963231949966635800852425193221658914799 60 19987556196019746934559490493908126130478310916985676680825131675475834956269416368131390860400524736253193350877031424890618150894631360660555214791233380817082613242334649401913706349419529298111678642103008577869651397737137307296898997921920272507265954704602147279649946742171997814500423616836127877151 59 51096222195660998838214993398008975443334226469462987938620835940031595422906389948456714314184250584134675031854562918540111185432877967886125365843859202759838619358876321717841898972235167208334603406133491230325950874308071748186279415332768724277308777107769815375150668126847491101640368755019633726889 57 29134244853493331789283603393275291749816044468350702102035506094598790040927938861054634777247830931517686010741339628812116985594232674807263027901600624507630247209184903517192048488176261028761389768656154493158817886581472185760507276853927467270445108103128473821519705668231154797667164681995129099167 44 22727001808817855311403725351156659724989158069800490466458013816315274831050097254851934829809436415084558805190061876535460171481477325886587862814504906096266519469387070277858969077815631009037077538503164118774110740593006218494447633084714757032153557681184383300445044005450878303829523921113090598503 43 12809420335059752622795672675980615147379433503921952871001570329869909602631152404784101902235852407354985529217839517914337978763562477704639713177361527151286904208185025322596545149058203315249298373136118690015234673764106807029822628760444420022929741931249845208516150129504338691005143546218303736485 39 3929570815133494377565674564390309833497202447403079059880445103091097112439963260471815756880162820614427515327977655020489262502104373204431222035394513353720509807520161739252076395126436615051937945259162514387773880075644161755707728744548141441713692993486773337542283702554850976267025978523835156103 31 40134547635227845599825339690894195012168718754712945141544421186023480430553150024357178615922032531442839979802093306933346913584778658886938008884216860952509344521015417521265603939411082620539473525127363853503284782317720170238435878533613693578512044166590440262304835466215502510526120232032001658845 28 19492166218065210361696686707896525268020417715191233863834594410819422493908382086802419877050654000223876689075138373828891333608984761550312273195513504605801530063487641725099161221148773827710266506625126250751074980206372410832787410270736779064975681240662166847411633904532223257736996555482185275717 26 35757511882733355483839947542352804611289303760086802899974215637660071779650145686478637770001786118916493988988448569553752725399372273917548305878712872685951566425456575300012758123702510007669248383698343577662182410702363875166254773789867158011011670420550839163044289826725125706067556429856779495564 25 14576332930836336401134272222550882346965368092028955000954694875179130873398333216454729664378847576041041506775766783029984889520769135364408129680069043197669185727467506703395296323412031069601024043172225202033251709886245288125871615751041310682693335390022558588465347411736471596258937782467179701363 24 15799025644615822656801740434122556637212995922559332084222280459000654656427689834064128147572871045216617743273426836990308480455737076816410648044480511949442083909138576214738788738048193643029632245738932831021072125057111936960522329562306867802898765387374026585757497606153328226325713384411664479472 18 34220770932871364013976724839545041417474666615300575941746695940071552482886462087439379719184240006479394129946558717984964307444237521284361087031583504037093765914149168694482266218524635203263596760639253965500892625668716519628460563860957678979373258071483670494006067028836185890388591731283716604832 16 21825516420085786633620414923499927809866106375209997536887923519665612310710893091548347638116562999505810709467483467910561336083489137335015281764912210385860293937794761219080479166302700347936082258520119437027319181174057624695351433300415797052703957131305247757258587758932996789777812701543305273524 16 2491776416157094729247228546388058805100982106803126656760544775570831165844468695126053157622604400534191689984239642501431889749664796813015093832003828115405081489372948999096884256544945626310866557608968099061130574640407181237631369536699135922165700470873033015069995508536990789193832860645907343986 12 12932315605361356260109350737202295649066381035837249252185795202913980480440863417983883037159810577739986004162343142150811156736478717833534910573828843843135123757197342268856313199793884733585941943828474996180460900240457279087457908434717560236156491751130556115885434115169341757101655831937772066303 11 27576274928869221620126245883590920739381444228403264811604678585326136261919043025439432380393614033747213164606047970194501234144690982453937415512291833747115414764529517980671948859099514533322022692971474660454113892401294955396004739513550951184454650026652626364585678702730119565114784074733394949336 9 1176875645989444228120683125555162464459775615749992327233861740655598304185200372099710632670669740275928889234588484578424676523579010677635946710527054032662591517295007580344076297705713808521731216834723911361610732077241004086348355880037625191238102086425263717843500661215346831687259608549125530807 5 52840621689121797895256363389338274694450461789829175087736646052885972599541176587393339836186116798179639665528641843475425650830795547188378088601848535424795824136246287654182750346069524432086206082201048105736692531622222816403756012329174735009131234941877426201644907061786470186383501136594209222405 4 39071839511948638988080907036852746654085273366404837973213329692814484554408908523546999438831321352816110395822192272922701572846039352688552458816923896373772472819785936751685465282644216513301671688378689515602296293965301386883552780271126801778759956341143215735911106078099952795281272294184101222894 4 50154500011327049415150110613714558756986965132059956858621967629544808661996323441483612798709196285670748400127394046198652122647065373883652074401488461140240807698457285933739509452128499026773680398001271333305476126787388797879767072284116978372707084228927669307533874093727830120482310649071798909223 2 38802989341210530457378237385843973124921316122128304138276723482825938449328688522058677634210417960328667542939425659386994898427574509818766303473446802692515345332427976398389916234534200995301483992776549890379656184952685366723722458147873775598641647772939243953968981681779761004069962129149532525241 1 22898825038689625715487339309684047496088088286379048682632329486928624317960893419908872575544541743109960984821146081005860923057711786824611353925189608095318119267730739890712604642525421504696090823029339278724706589872240410882755614978083387780278129076143536569517954666638462991000336176075614807880 1 32673744615799712487218586784858666657615496658878295924699304141157435241805321678825497057203170526047413088723755930727839423037832480520297361079311603101279858983310265841651031957166707800564192379099456051456890378670008176632913201998572911894331423107676669652519124282681545581828946130363768378027 1 47570760099332538630074246588266937941307517820515142582135658748192399272005539496578959306267521195254022986091052760574620123103280649808061816984656151624030812710123783651478012545264847339309664114861788542619162083048255751820685971177031319072241032895991001430158963380558156843892347920250300986171 1 930044605345939201480478373277413008095802574786191190905074555539638928544692229073288242327962810058855318227403376039279203240132190223148619950893934472181209933145274613718642434124893448103578245304758494945314633484270441574356508120432815219715951750624307928142686494962369790708881847436477126536
出現頻度が最も高い文字を[space], 2番目に高い文字をeと仮定し,を求めます.
RSAではを以下のように計算します.
そのため,は次のように表すことができます.
したがって,のGCDを計算すれば,
を求められます.
によっては上手くいかない場合もありますが,FactorDBになげてあげればなんとかなります(?)
from Crypto.Util.number import GCD e = 0x10001 # space c1 = 20208833413145256771572368688664189468143545391164156105460199405734708819434076552216759462791005323959520084836115140504630769338040681414876273881508073569978297202819424741264124574247314460725471331318820764161255759739403546471531796892912689444815674366578876801858606344288032682809803593429599353582 # e c2 = 18218008764547928666818612371880437638590536088955960541217152923316878781023941482176664233664036926858934241182299360237997946767992823894857524509996035969116730840866188239505740019205603874588738160712590494329532220987368292751238523333362017189147629358097781421283836794237708493190976028985458918909 k1_n = pow(ord(' '), e) - c1 k2_n = pow(ord('e'), e) - c2 n = GCD(k1_n, k2_n) print(n)
106722289100028106333442730393961825779877604605535086872680596840706953799749221494444758643089316420424547317489248364875777056603635051238648525173511505121444368345778603560664552707224335172588518202681498311878808031409074943854136615164899327815566628813453310510081039328308224995882181249171863662094
邪魔な係数がついてるのでFactorDBになげます
53361144550014053166721365196980912889938802302767543436340298420353476899874610747222379321544658210212273658744624182437888528301817525619324262586755752560722184172889301780332276353612167586294259101340749155939404015704537471927068307582449663907783314406726655255040519664154112497941090624585931831047
が分かればあとはやるだけです.
import string with open('cipher.txt') as f: ciphers = list(map(int,f.read().strip().split(','))) e = 0x10001 n = 53361144550014053166721365196980912889938802302767543436340298420353476899874610747222379321544658210212273658744624182437888528301817525619324262586755752560722184172889301780332276353612167586294259101340749155939404015704537471927068307582449663907783314406726655255040519664154112497941090624585931831047 flag = '' for c in ciphers: for s in string.printable: if pow(ord(s),e,n) == c: flag += s break print(flag)
> python solve.py when i was in college in the early 70s, i devised what i believed was a brilliant encryption scheme. a simple pseudorandom number stream was added to the plaintext stream to create ciphertext. this would seemingly thwart any frequency analysis of the ciphertext, and would be uncrackable even to the most resourceful government intelligence agencies. i felt so smug about my achievement. years later, i discovered this same scheme in several introductory cryptography texts and tutorial papers. how nice. other cryptographers had thought of the same scheme. unfortunately, the scheme was presented as a simple homework assignment on how to use elementary cryptanalytic techniques to trivially crack it. so much for my brilliant scheme. from this humbling experience i learned how easy it is to fall into a false sense of security when devising an encryption algorithm. most people dont realize how fiendishly difficult it is to devise an encryption algorithm that can withstand a prolonged and determined attack by a resourceful opponent. here is the flag. when it comes to crypto or carpet never roll your own
HackTM{when_it_comes_to_crypto_or_carpet_never_roll_your_own}
Bad keys [197pts, 82solved]
I captured this encrypted message a while ago.
Today, I got into their network and managed to take a snapshot of their key server. I don't think more than 10k messages have been sent between when I captured the message and when I took the snapshot.You can access the snapshot here:
nc 138.68.67.161 60005
flag.enc
2255296633936604604490193777189642999170921517383872458719910324954614900683697288325565056935796303372973284169167013060432104141786712034296127844869460366430567132977266285093487512605926172985342614713659881511775812329365735530831957367531121557358020217773884517112603921006673150910870383826703797655
RSA_PUB
(65537, 2318553827267041599931064141028026591078453523755133761420994537426231546233197332557815088229590256567177621743082082713100922775483908922217521567861530205737139513575691852244362271068595653732088709994411183164926098663772268120044065766077197167667585331637038825079142327613226776540743407081106744519)
rsa.py
def int_to_bytes(x: int) -> bytes: return x.to_bytes((x.bit_length() + 7) // 8, 'big') def int_from_bytes(xbytes: bytes) -> int: return int.from_bytes(xbytes, 'big') def egcd(a, b): x, y, u, v = 0, 1, 1, 0 while a != 0: q, r = b//a, b % a m, n = x-u*q, y-v*q b, a, x, y, u, v = a, r, u, v, m, n gcd = b return gcd, x, y def enc(key, plaintext): e, n = key m = int_from_bytes(plaintext.encode()) return pow(m, e, n) def dec(key, ciphertext): d, n = key plain = "" return int_to_bytes(pow(ciphertext, d, n)) # keys: Public: (e,n), Private (d,n) def generate_keypair(p, q): e = 65537 n = p * q phi = (p - 1) * (q - 1) gcd, d, b = egcd(e, phi) # Keys:((pub), (priv)) return ((e, n), (d, n)) ''' #demo usage message = "Hello there" k = generate_keypair(p, q) c = enc(k[0], message) p = dec(k[1], c) print(k) print(c) print(p) '''
> nc 138.68.67.161 60005 Starting key server from snapshot #8055 ... Enter 'k' to generate the next key > k Your RSA keys: ((pub),(priv)) ((e,n),(d,n )) ((65537, 88051162316131292469465204252856397334672387723480165865180209633514313755050858659874111484364935930429293893604430655271246592259685939378371663525862168708113157831045417450025798105829762942546449002712798656762717893350159819387064343998841406565258963717201919776878018099330853017769765709546840465391), (13785998390616341792104955381518218610114490599670872666472590003349106206273965251826727771198996102692143135057678303153001530176490187588102470962034751578717101950870557505740211239981422511461496036836191640241180486060736508366430751200887711980385485178550105810859250514938906705892872045147076991289, 88051162316131292469465204252856397334672387723480165865180209633514313755050858659874111484364935930429293893604430655271246592259685939378371663525862168708113157831045417450025798105829762942546449002712798656762717893350159819387064343998841406565258963717201919776878018099330853017769765709546840465391)) Enter 'k' to generate the next key > k Your RSA keys: ((pub),(priv)) ((e,n),(d,n )) ((65537, 68696651523524886996746044827480935717451768623875675099302556827709043638169999205502403603716684986196543586683629731565080106015927556053810071313682866628297219680434241485867723251895065319814500201735165760665981249615377439393912913231508229191283667182702486243040141529768112697952740881029882182319), (22077435256244276819589929294236896227794515323497710742656979292692797612144842200074639130590060869116248852140479567362310102581861638244126946946134064151533818278112738055020446270162748413472435173777163134588017480420530339765687001268867734569053232104607731464548965788273285273292499279515732565313, 68696651523524886996746044827480935717451768623875675099302556827709043638169999205502403603716684986196543586683629731565080106015927556053810071313682866628297219680434241485867723251895065319814500201735165760665981249615377439393912913231508229191283667182702486243040141529768112697952740881029882182319)) Enter 'k' to generate the next key > k Your RSA keys: ((pub),(priv)) ((e,n),(d,n )) ((65537, 20276323319456892879455257682366324009209759965427225413973361649583409066512491277305221081940520241651390596794816867021769763335645211474994929467340648342448448284630153254252729554022960439415263547110052473132122669553965492432062189867115904797143294425509010060159831766772400300269022931502798309789), (-2109094039530915952198704420719459706284738906027395145445418715614234701106484169818418482927026358962685653880254918328385560472085896617560163482900668412305209608284106657680807569969879092362057886913677606838979841458151309216634915568901280390304084676048711235180025063399453575134002608820163981723, 20276323319456892879455257682366324009209759965427225413973361649583409066512491277305221081940520241651390596794816867021769763335645211474994929467340648342448448284630153254252729554022960439415263547110052473132122669553965492432062189867115904797143294425509010060159831766772400300269022931502798309789))
アプローチ:鍵生成処理をGuessing
タイトルから鍵生成に問題があると分かるのですが,鍵生成処理が公開されていないため,Guessingする必要があります.
- 問題文のencrypted messageをキャプチャしてから送信されたmessageは10k以下という記述
- 操作説明のEnter 'k' to generate the next keyという記述
上記の記述から鍵生成では何らかの漸化的な処理を行っていると考えることができます.
そのため,ここで,一旦を構成する
または
が以下のようになっていると仮定します.
次に,適当に生成したPrivate Keyのサンプルのから
を計算し,
から
を求め,仮定の妥当性を確認します.
import gmpy e = 0x10001 n1 = 88051162316131292469465204252856397334672387723480165865180209633514313755050858659874111484364935930429293893604430655271246592259685939378371663525862168708113157831045417450025798105829762942546449002712798656762717893350159819387064343998841406565258963717201919776878018099330853017769765709546840465391 d1 = 13785998390616341792104955381518218610114490599670872666472590003349106206273965251826727771198996102692143135057678303153001530176490187588102470962034751578717101950870557505740211239981422511461496036836191640241180486060736508366430751200887711980385485178550105810859250514938906705892872045147076991289 k1 = int((e * d1) / n1) phi1 = (e * d1 - 1) // k1 p1_plus_q1 = n1 + 1 - phi1 p1 = (p1_plus_q1 + gmpy.root(p1_plus_q1**2 - 4 * n1,2)[0])//2 q1 = n1 // p1 n2 = 68696651523524886996746044827480935717451768623875675099302556827709043638169999205502403603716684986196543586683629731565080106015927556053810071313682866628297219680434241485867723251895065319814500201735165760665981249615377439393912913231508229191283667182702486243040141529768112697952740881029882182319 d2 = 22077435256244276819589929294236896227794515323497710742656979292692797612144842200074639130590060869116248852140479567362310102581861638244126946946134064151533818278112738055020446270162748413472435173777163134588017480420530339765687001268867734569053232104607731464548965788273285273292499279515732565313 k2 = int((e * d2) / n2) phi2 = (e * d2 - 1) // k2 p2_plus_q2 = n2 + 1 - phi2 p2 = (p2_plus_q2 + gmpy.root(p2_plus_q2**2 - 4 * n2,2)[0])//2 q2 = n2 // p2 print(gmpy.next_prime(p1) == p2)
> python check.py True
どうやら,素数生成にを利用しているという仮定は正しいようです.
したがって,または
を10k程度行えば,
RSA_PUBのを構成する
または
を取得できることが分かります.
Sage(previous_prime)を利用して,を求めると以下のようにflagを得ることができます.
sage: p = 12117717634661447128647943483912040772241097914126380240028878917605920543320951000813217299678214801720664141663955381289172887935222185768 ....: 875580129863163 sage: n = 23185538272670415999310641410280265910784535237551337614209945374262315462331973325578150882295902565671776217430820827131009227754839089222 ....: 175215678615302057371395135756918522443622710685956537320887099944111831649260986637722681200440657660771971676675853316370388250791423276132267 ....: 76540743407081106744519 sage: for i in range(10000): ....: if n % p == 0: ....: print(p) ....: break ....: p = previous_prime(p) ....: 12117717634661447128647943483912040772241097914126380240028878917605920543320951000813217299678214801720664141663955381289172887935222185768875580128178823
from Crypto.Util.number import * c = 2255296633936604604490193777189642999170921517383872458719910324954614900683697288325565056935796303372973284169167013060432104141786712034296127844869460366430567132977266285093487512605926172985342614713659881511775812329365735530831957367531121557358020217773884517112603921006673150910870383826703797655 e = 0x10001 n = 2318553827267041599931064141028026591078453523755133761420994537426231546233197332557815088229590256567177621743082082713100922775483908922217521567861530205737139513575691852244362271068595653732088709994411183164926098663772268120044065766077197167667585331637038825079142327613226776540743407081106744519 p = 12117717634661447128647943483912040772241097914126380240028878917605920543320951000813217299678214801720664141663955381289172887935222185768875580128178823 q = n // p d = inverse(e, (p-1)*(q-1)) m = long_to_bytes(pow(c,d,n)) print(m)
> python solve.py
b'HackTM{SanTa_ple@s3_TakE_mE_0ff_yOur_l1st_4f2d20ec18}'
HackTM{SanTa_ple@s3_TakE_mE_0ff_yOur_l1st_4f2d20ec18}
まとめ
- 簡単な問題しか解けなくて悲しくなった
- Forensics, Revにももう少し時間を割けばよかった
RiceTeaCatPanda CTF 2020 Write-up
はじめに
2020/01/20 ~ 2019/01/25に開催されたRiceTeaCatPanda CTFにチーム(NekochanNano!)で参加しました.
成績
チームとしては29問解いて34位でした (1323チーム中).
今回は自分が解いた6問のWrite-upを書きます.
Reverse Engineering
What's the Password: Revisited [300pts]
There's a password somewhere...
> file whats-the-password-revisited whats-the-password-revisited: ELF 64-bit LSB shared object x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, for GNU/Linux 3.2.0, BuildID[sha1]=36f742e6516c60be312a3b60eb7e4f3fbf703161, stripped
アプローチ:Ghidraでデコンパイル
配布ファイルを実行するとパスワードの入力を求められます.
> ./whats-the-password-revisited Whats the password? satto1237 Hey, that's not right!
配布ファイルをGhidraでデコンパイルして,内部処理を確認すると
入力文字列に対して排他的論理和をとった値とDAT_00301020を比較していることが分かるので後はデコーダを書けば終わりです.
undefined8 FUN_001007c0(void) { // [snip] byte local_3b [20]; // [snip] __fgets_chk(local_3b,0x16,0x1c); // [snip] lVar1 = 0; do { if ((int)(char)(&DAT_00301020)[(long)(int)lVar1 * 0x50] != ((int)(char)(local_3b[lVar1] ^ 0x32) + 1U ^ 0x32)) { puts("Hey, that\'s not right!"); /* WARNING: Subroutine does not return */ exit(0); } lVar1 = lVar1 + 1; } while (lVar1 != 0x14); // [snip] }
# DAT_00301020 DAT = [0x3a, 0x31, 0x52, 0x30, 0x34, 0x36, 0x52, 0x30, 0x33, 0x5c, 0x3a, 0x51, 0x73, 0x30, 0x35, 0x45, 0x5c, 0x31, 0x5a, 0x34] passwd = '' for x in DAT: passwd += chr(((x ^ 0x32) - 1) ^ 0x32) print(passwd)
> python solve.py 50m371m32_5Pr34D_0U7
> ./whats-the-password-revisited
Whats the password? 50m371m32_5Pr34D_0U7
Nice job! Here's your flag: rtcp{fL492_r_50m371m32_5Pr34D_0U7}
rtcp{fL492_r_50m371m32_5Pr34D_0U7}
screams [1500pts]
You know what, you fix this lol
https://github.com/JEF1056/riceteacatpanda/tree/master/screams%20(1500)
aaaaaaaaaaaaaaaaaa.wav
> file aaaaaaaaaaaaaaaaaa.wav aaaaaaaaaaaaaaaaaa.wav: RIFF (little-endian) data, WAVE audio, stereo 44100 Hz
ur-worst-nightmare.py
import cv2 as a import soundfile as b import random as c import numpy as d from tqdm import tqdm as e import os as f import binascii as z g, h = a.imread("pls-no.jpg"), b.SoundFile("oh-gawd-plsno.wav", 'r') i, j = g.shape[0], 0 k=d.zeros((i*i,2), dtype=d.float64) l, m = e(total=i*i), h.read() l.set_description(" nuKiNG") h.close() u=True t = b'9\x04\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00' v = b'@\xe4\x10\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00' for n in range(0,i): for o in range(0,i): if u == True: p, q, r = g[n][o][0], g[n][o][1], g[n][o][2]; p, q, r = str(p), str(q), str(r) # me me me while len(p) < 3: p="0"+p while len(q) < 3: q="0"+q while len(r) < 3: r="0"+r#eeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeee result = p+q+r for w in range(0, j+1): x=z.b2a_uu(t); y=z.b2a_uu(v) t = z.a2b_uu("0.00") # ww v = z.a2b_uu("-0.00") s=c.randint(0,1) if s == 0: k[j]=(m[j][0]*2,float(x.decode()[:-2].strip(" ")+result)) if s == 1: k[j]=(m[j][0]*2,float(y.decode()[:-2].strip(" ")+result)) j+=1 #b l.update(1) #wow 0 then b.write('out.wav', k, 44100, 'FLOAT')
アプローチ:頑張ってエンコーダを読む
aaaaaaaaaaaaaaaaaa.wavとur-worst-nightmare.pyが配布されます.
ur-worst-nightmare.pyはエンコーダで,恐らくaaaaaaaaaaaaaaaaaa.wavはフラグ画像が埋め込まれた音声ファイルだと考えられます(guessingしたくないのでファイル名を)out.wavに」してくれ
ur-worst-nightmare.pyの処理を簡単にまとめると以下のようになります.
- フラグ画像の読み込み
- 音声ファイルの読み込み
- フラグ画像のBGRの各ピクセル値を取得
- 各ピクセル値を3桁で0パディング
0.00または-0.00と0パディングしたピクセル値を連結して小数化- 小数化したピクセル値を
wavに埋め込み
これらを踏まえてソルバを書くこと以下のようになります.
from PIL import Image import soundfile img = Image.new('RGB', (500,500)) wav = soundfile.SoundFile("aaaaaaaaaaaaaaaaaa.wav", 'r') wav_data = wav.read() wav.close() count = 0 for y in range(500): for x in range(500): b = int(abs(wav_data[count][1] * 100000)) g = int(abs(wav_data[count][1] * 100000 * 1000)) % 1000 r = int(abs(wav_data[count][1] * 100000 * 1000 * 1000)) % 1000 count += 1 img.putpixel((x,y),(r,g,b)) # img.show() img.save('./flag.jpg')

rtcp{uh_oh_sisters_342}
General Skills
Treeeeeeee [200pts]
It appears that my cat has gotten itself stuck in a tree... It's really tall and I can't seem to reach it. Maybe you can throw a snake at the tree to find it?
Oh, you want to know what my cat looks like? I put a picture in the hints.
treemycatisin.7z
> file treemycatisin.7z treemycatisin.7z: 7-zip archive data, version 0.4
アプローチ:ハッシュ値
treemycatisin.7zを解凍すると27847のディレクトリと1337のファイルを含んだbigtreeフォルダを得ることができます.

bigtree内のファイルを眺めるとどうやら2種類のjpgファイルが大量に存在することが分かります.


1つ1つ調べるのは手間がかかるのでハッシュ値を利用してサクッと目的のファイルを検索します.
> mkdir jpg
> find ./bigtree -type f | grep "\.jpg$" | xargs -J% cp -p % ./jpg
> md5 ./jpg/*.jpg | awk '{print $4}' | sort | uniq -c
655 2d7b81239b77deb7fbda026d9521939b
681 49390dd9695e7ab7c49fbea6697bc1a9
1 aeb3e033f8bdbf2ec44fda714da72f77
> md5 ./jpg/*.jpg | grep aeb3e033f8bdbf2ec44fda714da72f77
MD5 (./jpg/ENP92.jpg) = aeb3e033f8bdbf2ec44fda714da72f77
> open ./jpg/ENP92.jpg

RTCP{MEOW_SHARP_PIDGION_RICE_TREE}
Cryptography
HOOOOOOOOOOMEEEEEE RUNNNNNNNNNNNNN!!!!! [50pts]
AND JAKE IS ROUNDING THE BASES
HE PASSES BASE 32!!!
HE ROUNDS BASE 64!!!!!!!
WE'RE WITNESSING A MIRACLE!!!!!!!!!!!!!Just one more base to go ;D
Ecbf1HZ_kd8jR5K?[";(7;aJp?[4>J?Slk3<+n'pF]W^,F>._lB/=r
アプローチ:base85
base85でデコードするとflagになります.
rtcp{uH_JAk3_w3REn't_y0u_4t_Th3_uWust0r4g3}
View Hintを使わないと問題が見れないのってどうなの
Don't Give The GIANt a COOKie [100pts]
It was just a typical day in the bakery for Delphine. She was preparing her famous chocolate cake, when all of a sudden a GIANt burst through the doors of her establishment and demanded a cookie. Being the strong-willed girl she was, Delphine refused and promptly threw her rolling pin at the GIANt. Doing what any sensible being would do when faced with projectiles, the GIANt let out a shriek and ran out of the shop. Delphine smiled to herself, it was another day well done. But oh? What's this? It seems the GIANt dropped this behind while he was screaming and scrambling out of the shop.
69acad26c0b7fa29d2df023b4744bf07
アプローチ:md5のクラック
以下のオンラインツールを利用してmd5をクラックします.
rtcp{chocolate mmm}
15 [100pts]
Lhzdwt eceowwl: Dhtnwt Pcln Eaao Qwoohvw
Okw qsyo okcln bah'i fslo cl baht Dhtnwt Pcln dhtnwt cy yazwalw'y eaao ehlnhy. Dho sy co ohtly aho, okso zcnko dw fkso bah nwo. S 4vksllwt hmqasiwi s mkaoa slalbzahyqb oa okw ycow ykafvsycln kcy ewwo cl s mqsyocv dcl ae qwoohvw, fcok okw yosowzwlo: "Okcy cy okw qwoohvw bah wso so Dhtnwt Pcln." Sizcoowiqb, kw ksi ykawy al. Dho okso'y wgwl fatyw.
Okw mayo fwlo qcgw so 11:38 MZ al Xhqb 16, sli s zwtw ofwlob zclhowy qsowt, okw Dhtnwt Pcln cl rhwyocal fsy sqwtowi oa okw tanhw wzmqabww. So qwsyo, C kamw kw'y tanhw. Kaf ici co ksmmwl? Fwqq, okw DP wzmqabww ksil'o twzagwi okw WJCE isos etaz okw hmqasiwi mkaoa, fkcvk yhnnwyowi okw vhqmtco fsy yazwfkwtw cl Zsbecwqi Kwcnkoy, Akca. Okcy fsy so 11:47. Oktww zclhowy qsowt so 11:50, okw Dhtnwt Pcln dtslvk siitwyy fsy mayowi fcok fcykwy ae ksmmb hlwzmqabzwlo. Ecgw zclhowy qsowt, okw lwfy yosocal fsy valosvowi db slaokwt 4vksllwt. Sli oktww zclhowy qsowt, so 11:58, s qclp fsy mayowi: DP'y "Owqq hy sdaho hy" alqclw eathz. Okw eaao mkaoa, aokwtfcyw plafl sy wjkcdco S, fsy soosvkwi. Vqwgwqsli Yvwlw Zsnsuclw valosvowi okw DP cl rhwyocal okw lwjo isb. Fkwl rhwyocalwi, okw dtwspesyo ykceo zslsnwt ysci "Ak, C plaf fka okso cy. Kw'y nwoocln ectwi." Zbyowtb yaqgwi, db 4vksl. Laf fw vsl sqq na dsvp oa wsocln aht esyo eaai cl mwsvw.
tovm{v4T3Ehq_f1oK_3J1e_i4O4}
アプローチ:quipqiup
換字式暗号っぽいのでquipqiupに投げます.
rtcp{c4R3Ful_w1tH_3X1f_d4T4}
まとめ
- guessingが多すぎてしんどかった
- 途中で飽きてしまった(チームメンバのみなさん申し訳ないです)